Posted by Martijn Grooten on Dec 12, 2016
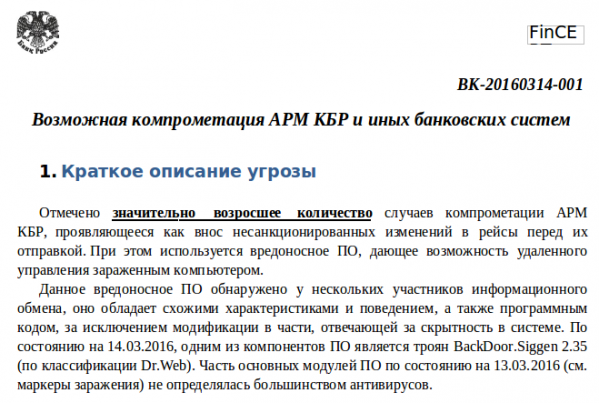
Today, we publish the VB2016 paper "Modern attacks on Russian financial institutions" (here in HTML format and here in PDF format) by ESET researchers Jean-Ian Boutin and Anton Cherepanov.
In it, they look at a number of groups that have performed sophisticated attacks against a number of Russian financial institutions. The work of these groups demonstrates the increasing sophistication and professionalization of cybercrime.
Today, the paper's authors have also published a blog post about the paper on ESET's We Live Security blog, in which they point out a misunderstanding in the way the Russian banking system works, which has led to a few news reports initially misreporting a theft at the Russian Central Bank while, in fact, the attack affected commercial banks.
We have also uploaded the video of the presentation to our YouTube channel.