Posted by Martijn Grooten on Dec 20, 2016
Last week, Microsoft published a paper on two attack groups, dubbed PROMETHIUM and NEODYMIUM, that targeted individuals in Europe and that both used the then unknown and unpatched vulnerability CVE-2016-4117 in Abobe Flash Player.
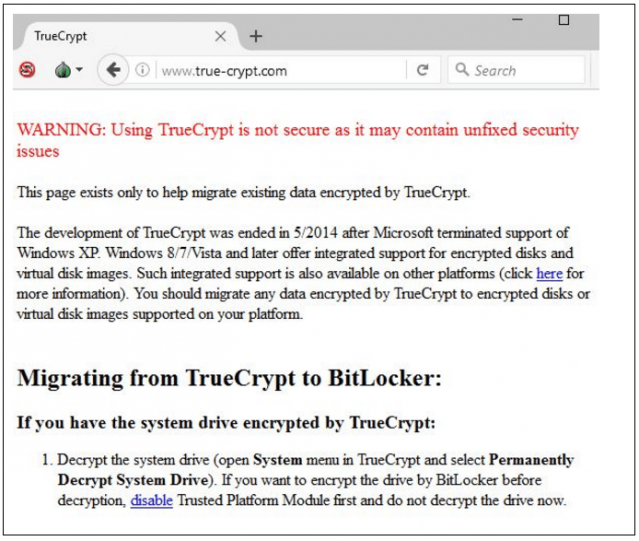
However, Microsoft wasn't the first company to write about the PROMETHIUM group and the Truvasys malware it used. At VB2016 in Denver, Kaspersky Lab researcher Kurt Baumgartner gave a presentation on the same group, which Kaspersky calls StrongPity, and which used watering hole attacks to target the users of encryption tools such as TrueCrypt and WinRAR.
We have now uploaded the video of Kurt's presentation to our YouTube channel. Since this was a "last-minute presentation" at VB2016, there is no written paper to accompany it, but Kurt did publish an accompanying blog post on Kaspersky's Securelist site.