Posted by Martijn Grooten on Jan 5, 2017
Many experts believe that ransomware is set to become an even worse problem in 2017 than it was in 2016 — which is rather bad news, given the damage it has already done.
Still, the problem could be much worse: a test of security products performed by Virus Bulletin in November/December 2016 showed that at least 199 out of every 200 emails with a malicious attachment were blocked by email security solutions (or spam filters). Add to this user awareness, which leads to attachments not being opened in many cases, or macros not being enabled, as well as endpoint security solutions preventing the malware from doing its work, and the end result is that only a very small percentage of the malware sent via email will lead to a malware infection.
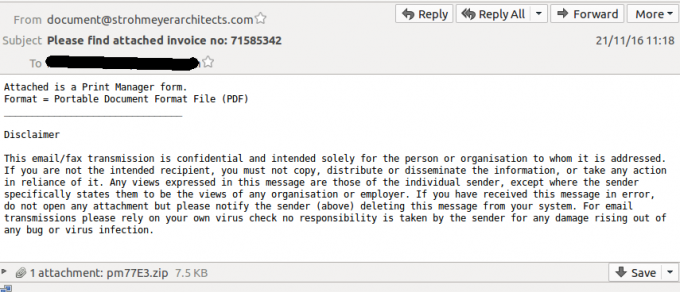
The test was run over a 19-day period, during which dozens of different malicious spam campaigns were seen, with the typical attachment being a malware downloader that would most likely have led to ransomware. No particular campaign stood out as being more difficult to block than others, suggesting that there is no silver bullet for spammers to bypass filters.
Of course, the fact that spam is sent out in large volumes means that even a very low success rate is sufficient for attackers to make a good return on investment — and thus to cause a lot of damage. But after previously having seen how well web security solutions block exploit kits (another common ransomware infection vector), it is good to be reminded of just how much more secure our digital lives are made by security products.
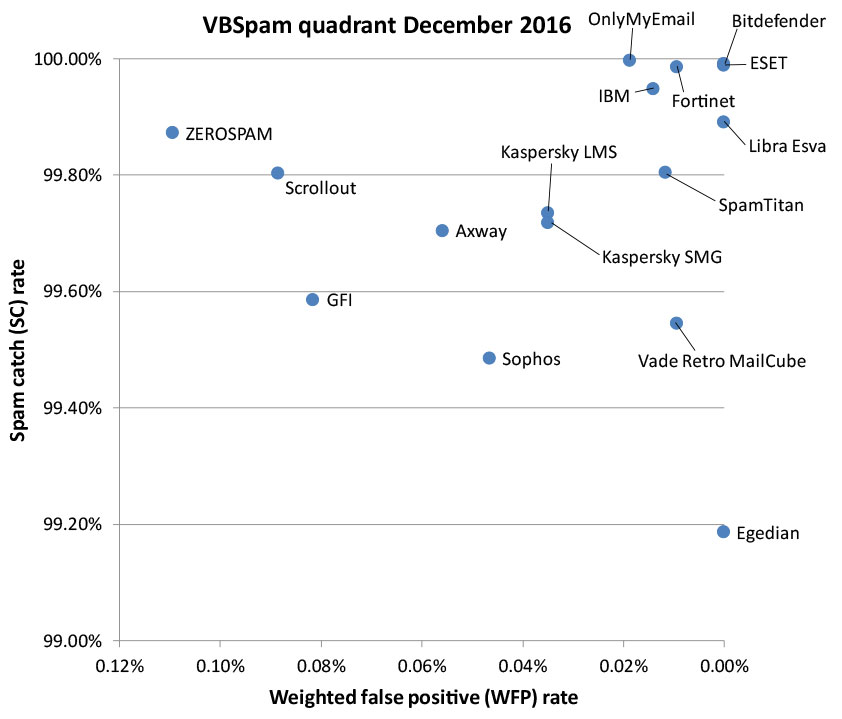
The test, which was part of our VBSpam series, also looked at how well solutions blocked spam in general and how well they managed to avoid false positives. 16 of the solutions tested achieved a VBSpam award, of which six — OnlyMyEmail, ESET, Bitdefender, Fortinet, Libra Esva and Vade Retro MailCube — reached the standard required to earn a VBSpam+ award.
For full details, read the VBSpam Comparative Review for December 2016, which also includes more details on the blocking of malicious spam.