Posted by Martijn Grooten on Feb 8, 2017
Every year, the Virus Bulletin conference programme includes a number of 'last-minute' papers: presentations on topics that are so hot, they are added to the programme only a few weeks before the start of the conference.
While the short time frame means there isn't enough time to add an accompanying written paper to the conference proceedings, there is often serious research behind the presentations and we are always glad to see such research being shared in another way. Early last week, CERT Poland published a long blog post on the 'Nymaim' banking trojan, detailing research that Jarosław Jedynak and Maciej Kotowicz presented in a 'last-minute' paper at VB2016 in Denver.
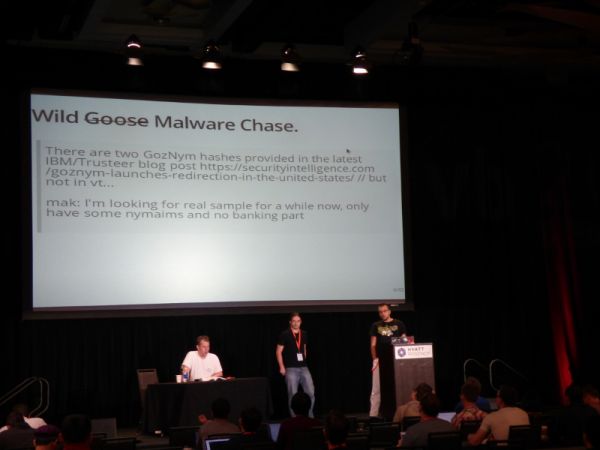
To coincide with their blog post, we have uploaded the video of Jarosław and Maciej's VB2016 presentation, in which they dive deep into the malware-dropper-turned-banking-trojan which, until very recently, was a serious plague in Poland.
Did you see that the Call for Papers for VB2017 (4-6 October in Madrid) has opened? Whether you've analysed a new banking trojan, or want to share how your organisation deals with security threats, we'd like to hear about it, so submit an abstract by 19 March! (As in previous years, a call for 'last-minute' papers will open in the summer.)