Posted by Martijn Grooten on Feb 9, 2017
The new UK government has passed a far-reaching surveillance law. The new US government has stripped privacy rights from non-citizens. Surely, those who have warned about the threat of Western intelligence agencies have a reason to feel vindicated.
In the post-Snowden era of IT security, many improvements to technology have made it a lot harder for the NSA and its allies to access our data and devices. "NSA-proof" has been an implicit (and sometimes explicit) goal of many new products and technologies, and that is a good thing: if we make something impenetrable by what is generally considered to be the most powerful possible adversary, we get protection against everyone else for free. And although Edward Snowden doesn't make the headlines very much these days, it is likely that recent events will further incentivise the drive for NSA-proof technology.
But we should make sure we don't forget that there are many very vulnerable groups and individuals who are concerned about very different kinds of attacks. Attacks that are at the same time both far more mundane and far more dangerous than anything the NSA could ever do.
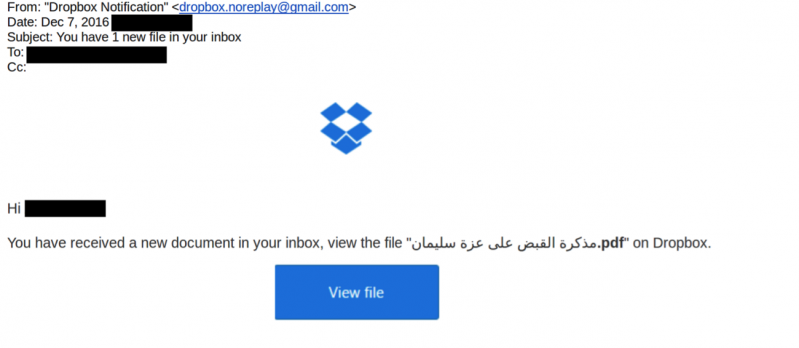
One such group are political activists and NGOs in countries that use a rather (il)liberal interpretation of the rule of law. Last week, Citizen Lab wrote about an ongoing campaign of spear-phishing emails against Egyptian NGOs. Technically, there is nothing special about this campaign; in fact, the attackers used an open source tool for the phishing websites. It is several steps beneath what the NSA is capable of. But the targeted nature of the attack means the emails can be made to look very credible to the recipients. And falling for the scam could lead to long prison sentences.
Another very vulnerable group consists of people dealing with abuse by an (ex-)partner. This is unfortunately a situation in which far too many people find themselves, and there is now often a digital component to this kind of abuse. The abuser often has physical access to the victim's devices and may be able to access the victim's online accounts, if not by knowing the password then by knowing enough information to allow them to reset it. This gives the victims a very different threat model from the one security experts tend to consider; consequently, the usual defences may not always work.
For the majority of my life, the primary threat I have modeled for is strange creepy men. Not every threat is a goddamn nation state.
— Eva (@evacide) February 3, 2017
Thankfully, these issues have been acknowledged. A team of Google researchers are calling for the tech community to consider the unique threat of "intimate partner abuser". They recently presented their findings at the Enigma conference in Oakland.
The aforementioned Citizen Lab does great work writing about the threats that civil society around the world is chasing; for his work, Citizen Lab Director Ron Deibert was recently named by Vice Motherboard as one of its "Humans of the year". The Iran Threats project does the same, but focusing on one particular area, and recently, a group of volunteers set up Security Without Borders, a project that aims to assist "journalists, human rights defenders, and non-profit organizations with cyber security issues".
Of course we should make our technology such that even the NSA can't read the emails I send to my mother, because what I write is simply none of their business. But in doing so we shouldn't lose sight of those most vulnerable in our digital world, because they need our help more than ever.