Posted by Martijn Grooten on Apr 10, 2017
Later this week, we'll be announcing the programme for VB2017, the 27th Virus Bulletin International Conference - a programme that we think is the best yet, and about which we are very excited. To give you just a sneak preview, we are thrilled to be able to announce today that the opening and closing keynotes will be delivered by John Graham-Cumming and Brian Honan, respectively.
In 1992, John Graham-Cumming wrote a Ph.D. thesis on secure systems, and quickly became one of the early experts on email spam; it was John who set up the 'Spammers' Compendium', which is now hosted by Virus Bulletin. His interest and expertise extends to anything 'geeky', as evidenced by his 2008 book 'The Geek Atlas', a travel book for nerds. In 2009, he led a successful campaign petitioning the British Government to issue an apology for its persecution of WWII code breaker Alan Turing, and he is the founder of Plan28, an organisation which aims to build Charles Babbage's Analytical Engine.
John, who has given a number of very well-received presentations at VB conferences in the past, is currently CTO of Cloudflare. As such, he recently made the news when the company was hit by the Cloudbleed vulnerability. The company's response to the vulnerability, which included a post-mortem written by John, the company's chief nerd, rather than by its PR department, received praise from many in the security industry. Details of Cloudbleed, as well as the lessons learned from the vulnerability, will be covered by John in his opening keynote address.
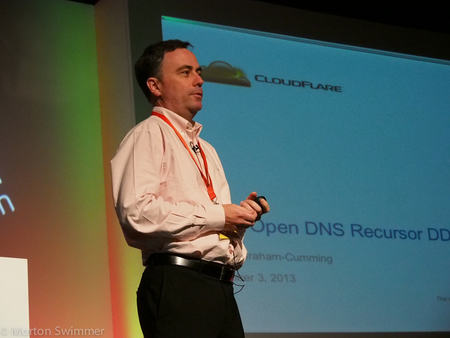
John Graham-Cumming.
At the other end of the conference, the closing keynote will be delivered by Brian Honan.
While most security experts share their thoughts and opinions from the ivory towers of research labs, this doesn't apply to Brian. As a security consultant he not only sees the threats organisations are facing, but he also sees the constraints organisations operate under when trying to fight these threats. He has 25 years' of consulting experience and shares his expertise with the likes of Europol's Cybercrime Centre, for which he has been a Special Advisor since 2013, and IRISSCERT, Ireland's national CERT, which he founded and still heads.
Brian organises the annual IRISSCON conference and for many years has organised the European Cybersecurity Blogger Awards. He is regularly quoted in the press and is very active both on Twitter and as a blogger. Last year, Brian was inducted into the Infosecurity Europe Hall of Fame, joining well-known names such as Mikko Hyppönen, Eugene Kaspersky and Bruce Schneier.
Watch out for the full programme for VB2017, which will be published later this week. Registration will open soon.