Posted by Martijn Grooten on Apr 28, 2017
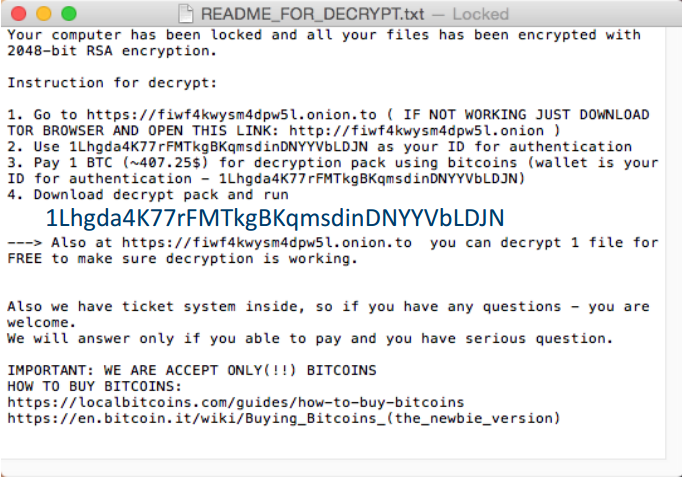
Though nowhere near as exotic as it was a few years ago, malware for OS X continues to attract researchers' attention. This was certainly the case for the KeyRanger ransomware and the Keydnap credentials-stealer, both of which spread through a compromised server of the legitimate Transmission BitTorrent client.
In a VB2016 last-minute presentation, ESET researchers Peter Kalnai and Martin Jirkal took a careful look at both instances. They also explained how they used the Volatility Framework to analyse the malware, and to create a plug-in to detect IoCs on memory dumps of compromised systems.
The video of Peter and Martin's presentation is now available to watch on our growing YouTube channel – where, incidentally, you'll also find a video from IBM researcher Martin Korman who, a year earlier, presented a paper on using Volatility to extract binaries from malware samples.
If you're interested in OS X malware, make sure you join us at VB2017 where Patrick Wardle (Synack) will discuss how to analyse such malware with a custom C&C server, while Tiberius Axinte (Bitdefender) will discuss the OS X component of APT28's XAgent. Peter Kalnai will be on the programme as well: together with his colleague Michal Poslusny, he will present a paper on how banking trojans make use of web browsers.
Registration for VB2017 is now open - register before 30 June 2017 to qualify for the early bird rate!