Posted by Martijn Grooten on Jun 23, 2017
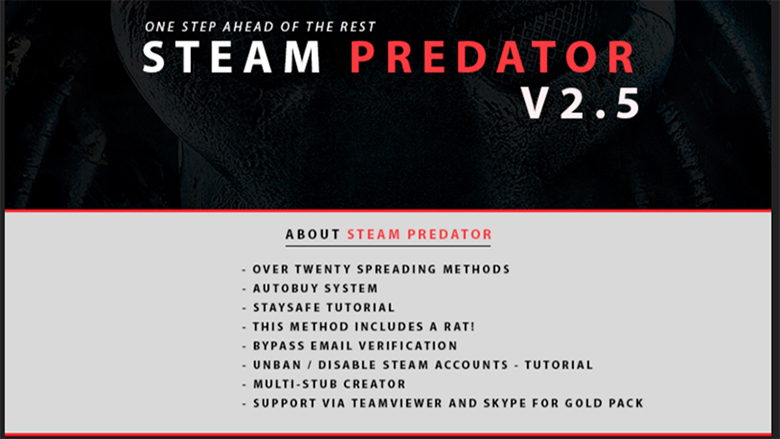
The online games market is huge, and the Steam platform is a huge player in that market. Users registered on the Steam platform use their credit cards to buy content, and willingly provide personal information to and exchange items with other network participants. Rather unsurprisingly, this has not gone unnoticed by cybercriminals, and a while ago they started to target Steam and its often valuable user accounts. Aside from (spear-)phishing, cybercriminals are also using malware variants known as 'Steam stealers' to seek out and harvest users' Steam credentials.
Last year, Kaspersky Lab researcher Santiago Pontiroli and PwC's Bart Parys presented a VB2016 paper analysing the malicious threats faced by Steam users and highlighting how organized criminals are making money with these profitable schemes. Today, we publish the paper in both HTML and PDF format. (Unfortunately, a video of their talk is not available.)
At VB2017 in Madrid, Bart Parys will be back with a look at the threat landscape from a very different perspective, when he will describe the threats faced by a multinational company like PwC. Meanwhile, for those with a particular interest in the area of gaming, another VB2017 paper, by Malwarebytes researcher Chris Boyd, will look at in-game advertisements, another possible threat faced by gamers.
VB2017 takes place 4-6 October in Madrid, Spain. Register before 1 July to receive a 10% Early Bird discount on full-price conference tickets.