Posted by Martijn Grooten on Aug 29, 2017
It is easy to be cynical about the security industry and its tendency to make ever bigger mountains out of molehills, but behind a thin layer of marketing, there are a great many people who really care about making the world a more secure place.
We have seen many examples of researchers from competitor companies working together in botnet takedowns, law enforcement actions against malicious actors, and the writing of more secure standards. The latest example of such a collaboration is the combined effort that led to the takedown of the WireX Android DDoS botnet.
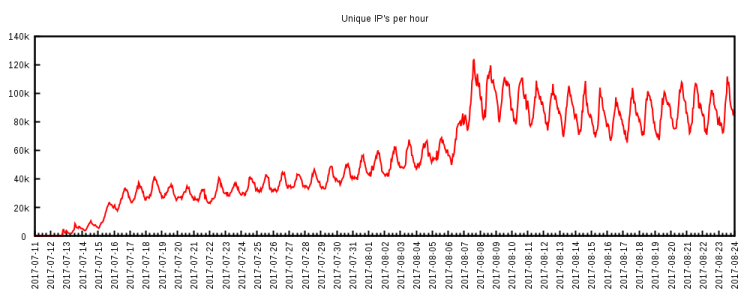
The number of unique IP addresses active in the WireX botnet every hour.
As DDoS botnets go, WireX wasn't particularly powerful, though still powerful enough to make many a website unavailable, thus making the associated ransom notes rather credible. It also wasn't particularly hard to detect, since it used random 26-character strings for the User-Agent header. Of course, this is something that could easily have been changed.
What made WireX rather unique though, was that it ran on Android devices and was made up of some 300 apps available on Google's official Play Store. These apps have since been removed both from the Play Store and from all infected devices.
The takedown effort was a combined effort from several companies, four of which — Akamai, Cloudflare, Flashpoint and RiskIQ — published the very same post-mortem blog post earlier this week. This is really the security industry at its best.
Virus Bulletin is always happy to help facilitate industry-wide collaboration, for example during the upcoming VB2017 conference. Don't hesitate to contact me ([email protected]) if you think we can be of help! And don't forget to register for the conference for a chance to meet with other researchers and build the connections that are essential for a more secure world!