Posted by Martijn Grooten on Sep 5, 2017
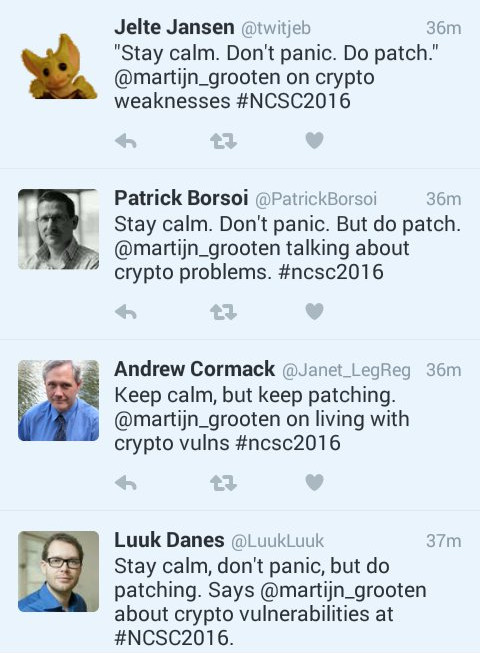
Sometimes a Tweet says more than a 50-minute conference presentation:
Bad TLS as an externally measurable metric for whether an organisation has a mature security process, sure. But it aint getting ya no shell.
— Metlstorm (@Metlstorm) September 4, 2017
This Tweet by Adam Boileau (best known outside New Zealand as the co-host of the Risky Business podcast) rather succinctly makes a point I also made during a number of conference presentations last year, including at RSA and NSCS One: most TLS vulnerabilities, even those that cause a media hype, are rather theoretical and are of little-to-no practical use.
If your bank supports RC4 on its website, you shouldn't be worried that someone may be able to decrypt the TLS connection: even the best known attack against RC4 requires several days of an active man-in-the-middle position. However, you should worry that your bank isn't following the latest and greatest security standards – if they haven't updated TLS, how do you know your personal data isn't accessible through an SQL-injection attack somewhere on their site?
This works both ways: while we have seen great improvements in recent years when it comes to software vendors taking security seriously, there are still many among them who wonder why they should spend money and effort on something that is essentially security window dressing by fixing vulnerabilities that are of little practical use.
Indeed, when speaking to security vendors, of whom there are many who haven't set up bug bounty programs (something which has become a bit of a pet peeve of mine), this is often the argument that higher management gives: vulnerabilities in security products are rarely exploited, while missed detections are a real problem.
But this misses the point: software security isn't a fixed state in which software is secure if no one exploits it. Rather, it is a process that involves continuous patching and updating in an attempt to always be one step ahead of the attackers. For sure, it does involve patching (and, through bug bounties, sometimes paying for) vulnerabilities that no one would ever exploit, but it does actually make everyone more secure in the long run, if only because no resources are wasted on making a decision on whether to patch.
At the upcoming VB2017 conference, Cloudflare CTO John Graham-Cumming will give a keynote presentation on Cloudbleed, a security vulnerability in Cloudflare's systems discovered and patched in February this year. Though Cloudbleed did leak actual memory, albeit for a very small percentage of requests, the lessons learned from Cloudbleed and its post-mortem analysis are valuable to any IT company, if not from the technical details then at least for the open approach the company when it came to fixing it.
VB2017 takes place in Madrid, Spain, 4-6 October. Register for VB2017 now to hear John's keynote, as well as more than 50 other speakers discuss the latest threats and how to defend against them.