Posted by Martijn Grooten on Sep 13, 2017
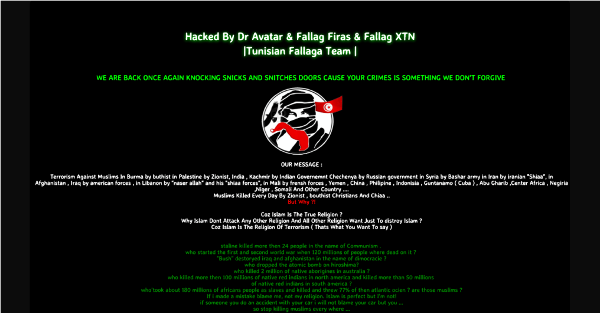
In March this year, following a political row between the Netherlands and Turkey, a large number of Dutch websites were defaced to display messages in support of the Turkish government. It was another example in a growing trend of socio-political motivated attackers defacing websites, or performing other kinds of hacks, to spread their message.
For security researchers, the first response in such a case might be to focus on the often poor security of the affected websites. But what about the attackers themselves: what motivates them? What tools do they use? How do these change over time?
Researchers Marco Romagna and Niek Jan van den Hout from The Hague University of Applied Sciences have written a paper – which they will present at VB2017 in Madrid – in which they provide a qualitative analysis of the motives and intentions of hacktivists, and a qualitative analysis of their modus operandi. It is one of those papers that will likely be used as a reference for many years to come, especially since there is no sign of the hacktivism threat going away any time soon.
To hear Marco and Niek Jan present their paper, and to hear more than 50 other speakers discuss the latest threats and how to defend against them, make sure you register for VB2017 (4-6 October, Madrid) now!