Posted by Martijn Grooten on Sep 29, 2017
Apart from the odd taxi driver loudly making the claim, the idea that "Macs don't get malware" has become something of the past. Nevertheless, most security researchers focus on Windows (and increasingly Android) malware, thus making malware that targets macOS still the odd one out.
Someone who for years has focused almost exclusively on researching Mac malware is Synack's Patrick Wardle. Patrick is often the go-to person for the press when a new Mac malware variant or attack is discovered, and he has spoken on the subject at the last three VB conferences, covering persistence methods; issues with Gatekeeper; and hacking webcams. He recently made the news when he found a zero-day vulnerability in the new macOS version, High Sierra.
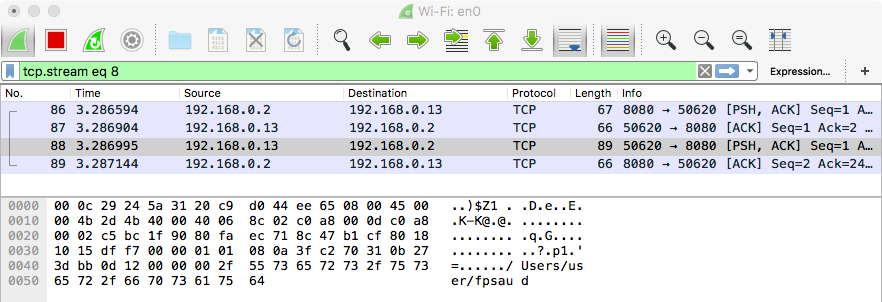
Next week Patrick will be back at the VB conference to present a long and detailed paper in which he analyses the mysterious 'FruitFly' malware, discovered earlier this year after having managed to stay under the radar for years. What is interesting about Patrick's analysis, and what makes his talk very relevant not just for Mac experts but for all security researchers, is that he set up a custom C&C server to find out what the malware is capable of.
<
For those who are interested in (advanced) Mac malware, Patrick's talk is followed by a presentation by Bitdefender's Tiberius Axinte on the Mac variant of APT28's 'XAgent' tool.
Registration for VB2017 remains open, but places are filling up fast – book now to avoid disappointment!