Posted by Martijn Grooten on Nov 2, 2017
As someone who spends most of his time talking to people who work for security vendors, I am always impressed by the amount of security research that takes place in the real world, at companies and organizations large enough to have teams dedicated to analysing the threats they are facing.
One such company is the French bank Société Générale, whose CERT I have come to know through its involvement in Botconf. So when, during VB2017, Alex Kouzmine and Frank Bitsch from this CERT approached me and asked if they could give a short presentation on their malware analysis framework, I was more than happy to allocate them one of the free slots in the Small Talk room.
They gave a short, but well-received talk on FAME, a 'Friendly Malware Analysis Framework' – an open source framework that should help make the important task of analysing the various threats an organization is facing both faster and easier. In the researchers' own case, for instance, the framework helps them determine quickly whether a new variant of a banking trojan targets their employer.
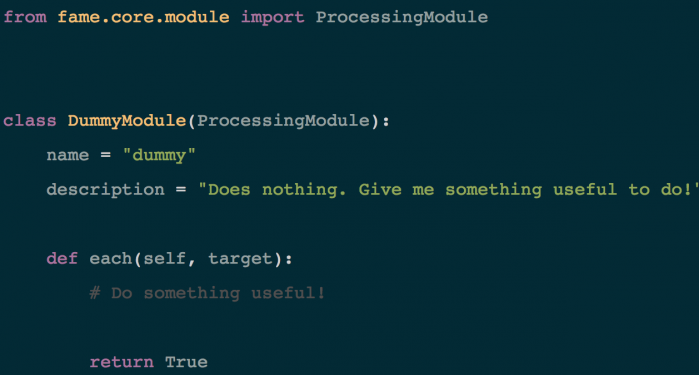
Creating a FAME module is as simple as creating a Python class.
Alex and Frank wrote a short paper to complement their talk, which we publish today both in HTML and PDF format.