Posted by Martijn Grooten on Dec 15, 2017
Earlier this week, we published the video of a VB2017 presentation on the Spora ransomware. Spora is hardly alone in this prominent threat type though, and one of the other major names in the world of ransomware is Cerber, which operates a successful affiliate scheme, making it 'The McDonald's of the underworld'.
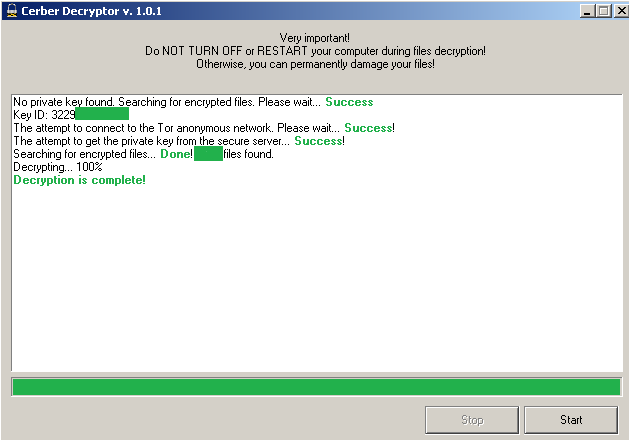
Last year, Check Point released a decryption service for the malware. For understandable reasons, at the time, the company did not provide details as to how they managed to decrypt the files, leading to guesses that it was a flaw in the encryption algorithm (a subject which Check Point researchers spoke about at VB2016), or maybe that the researchers were able to acquire the master decryption key.
At VB2017, the researchers went public for the first time with the details of their decryption algorithm – they were able to do so because an update to the ransomware meant their decryption tool had stopped working. In a paper written by Stanislav Skuratovich and presented in Madrid by his colleagues, Or Eshed and Yaniv Balmas, it was revealed that it was the decryption technology rather than the encryption algorithm that contained a weakness.
Today, we publish the paper 'Nine circles of Cerber' in both HTML and PDF format. We have also uploaded the video to our YouTube channel.