Posted by Martijn Grooten on Dec 1, 2017
Spam continues to be an important infection vector for many malware campaigns, but while a lot of attention is paid to the payloads delivered by these campaigns – Andrew Brandt's VB2017 talk on Trickbot being just one of many examples – few researchers study the botnets used to send the emails.
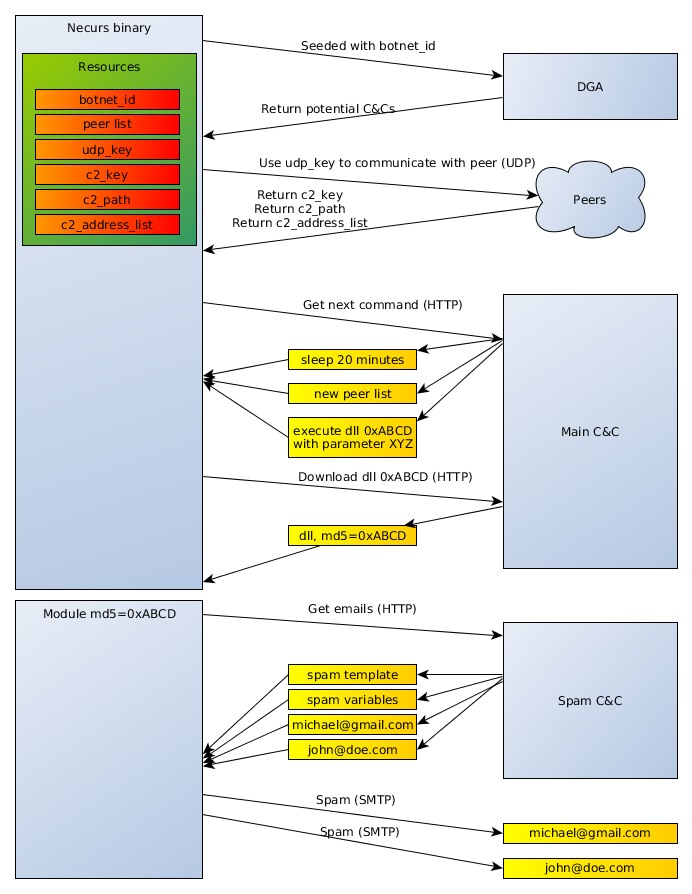
Bucking that trend are CERT Poland researchers Maciej Kotowicz and Jarosław Jedynak, who presented a paper on their research at VB2017. In their paper, "Peering into spam botnets", the researchers took a close and very low-level look at five major spam bots: Emotet, Kelihos, Necurs, Send-Safe and Tofsee.
Given the important role spam botnets play in the malware ecosystem, this paper is one that is likely to be referenced regularly, which is why, today, we have published the full paper in both HTML and PDF format.