Posted by Martijn Grooten on Dec 19, 2017
I have never been too keen on making comparisons between (advanced) cyber attacks and conventional war, as such comparisons tend to ignore the enormous human cost that comes with wars. That said, digital weapons do play an important role in global conflicts, military or otherwise, and thus it makes sense for them to be covered by the Wassenaar Arrangement, an export control regime 'for conventional arms and dual-use goods and technologies' that has been signed by 42 countries.
The Wassenaar Arrangement is quite controversial within the IT security community. For a combination of libertarian and pragmatic reasons, many working in the offensive side of security are opposed to a regime that they believe could prevent them from developing, using and selling their tools.
But these loudly voiced concerns overshadowed what, for me, was an even bigger concern: as it was previously worded, the Wassenaar Arrangement could be seen to seriously hinder the disclosure of security vulnerabilities, and the sharing of the command-and-control tools used by botnets.
I was thus pleased to read an op-ed in The Hill by Katie Moussouris (currently of Luta Security). Katie is a leading expert when it comes to vulnerability disclosure and has actively been involved in making the Arrangement work better for the security community.
She writes that the language of the Wassenaar Arrangement has been clarified, and that 'the specific cross-border sharing activities around vulnerability disclosure and security incident response are exempt from requiring export control licenses as dictated by Wassenaar'.
I am very pleased to learn this. Both vulnerability disclosure and coordinated botnet takedown are hard enough. One really wouldn't want to make them even harder by requiring the participants – many of whom are individuals or small companies – to wade through pages of export control paperwork.
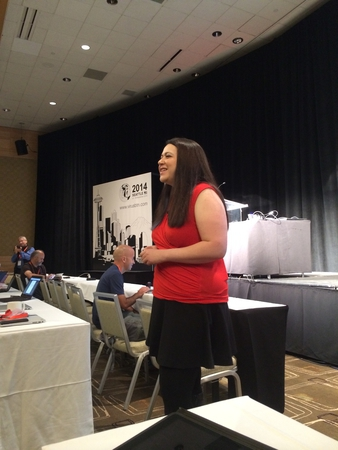 Katie Moussouris delivering the opening keynote at VB2014 in Seattle.
Katie Moussouris delivering the opening keynote at VB2014 in Seattle.