Posted by Martijn Grooten on Jan 16, 2018
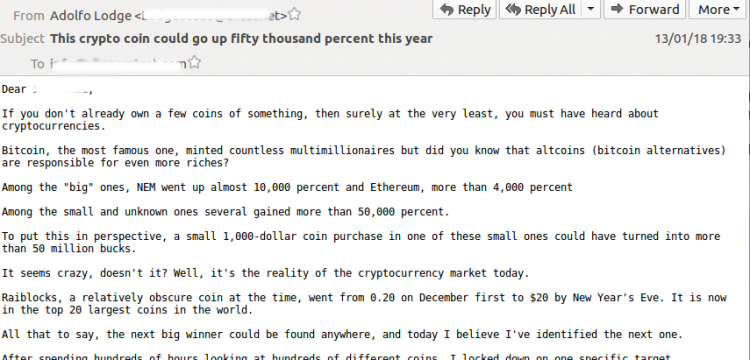
Cryptocurrencies have attracted the attention of cybercriminals for many years: as a relatively anonymous payment channel, as a target of their digital theft, and as a way to turn (temporarily) compromised systems into money-generating machines. Given the recent increases in the value of many such cryptocurrencies, it is not surprising to see them being promoted in a new incarnation of the old-fashioned pump-and-dump spam.
Having been alerted by a post on Conrad Longmore's Dynamoo blog, I looked at a large spam campaign that has been pushing 'Swisscoin', a lesser-known cryptocurrency and one with a rather dubious reputation.
I agree with Conrad that this has all the signs of a pump-and-dump campaign, where those behind it attempt to inflate the price of the currency in order to make a nice profit.
I found more than 35,000 emails from this campaign in our VBSpam test feeds, most of which were received through Abusix and Project Honey Pot. The large number suggests that it will have been a very large spam campaign, likely involving tens of millions of emails – which is not atypical of the Necurs botnet which delivered it. Last year, Necurs was behind another, more classic pump-and-dump spam campaign.
Necurs hasn't added any new infections for many years and its behaviour is in many ways reminiscent of the spam campaigns of the past: it sends emails from compromised home PCs that are running older and long-unpatched operating systems, makes no effort to bypass spam filters, and focuses on quantity rather than quality.
Indeed, despite there not being a tangible payload inside the email, such as a URL or an attachment, we found that all but a small number of emails in the campaign were blocked by every single email security solution, with several solutions blocking all of the more than 35,000 emails.
For those behind the campaign, the few emails that trickle through may be sufficient to make a decent profit – and if they're very lucky, some poorly programmed trading algorithms may make purchase decisions based on the mentions in the spam. But for the Internet as a whole, campaigns like this are largely just background noise.