Posted by Martijn Grooten on Jan 9, 2018
Of all the annual security reports and blog posts that look back at the previous year, that of Spamhaus is one I particularly look forward to, as it always comes with good and interesting data.
Though The Spamhaus Project is probably best known for its blacklists that are widely used for filtering spam, its researchers also keep track of botnet activity, and the non-profit publishes lists of IP addresses and domains used by botnets for command and control (C&C).
It is these C&C servers (or botnet controllers) that its Botnet Threat Report focuses on, and I think it's worth reading to get a good idea of how botnet owners choose hosting providers, top-level domains and domain registrars. It turns out that they tend to go for the popular ones.
The hosting provider most commonly used to host C&C servers is Amazon Web Services, though OVH (another very large hosting provider) is slightly more popular if one also includes compromised services used for the purpose. The most popular top-level domain used for C&C is .com, and the large Namecheap is most commonly used as a domain registrar.
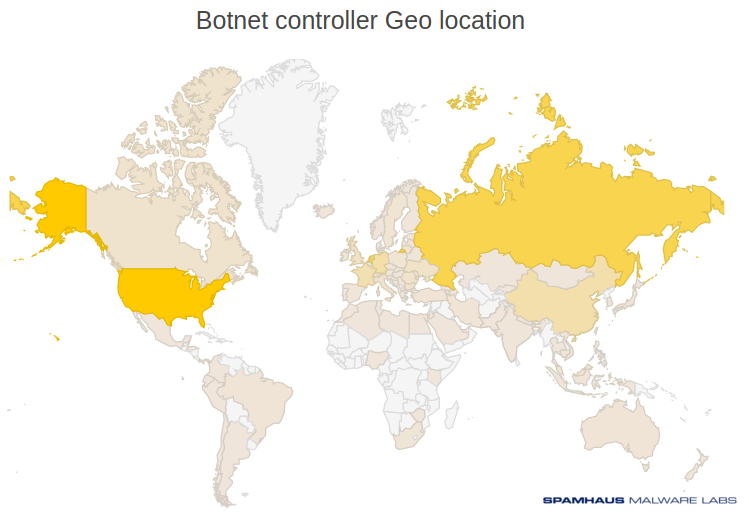
None of this should be very surprising, but it does show that fighting botnets is a lot more complicated than simply blocking all Russian hosting providers, all Chinese registrars and new gTLDs like .space: even if one is willing to ignore the many false positives such an approach no doubt generates, a whole lot will still fall through the maze.
The report does point out that there is a category of C&C servers that can't be tied to hosting providers, registrars and TLDs: those using Tor's Onion Services. To mitigate the risk of botnets using these kinds C&C servers, I agree with Spamhaus: Tor should be disabled by default and only be turned on for and by people who need it.