Posted by Martijn Grooten on Jan 25, 2018
In a surprise announcement, Google's parent company Alphabet has introduced Chronicle, a threat intelligence offering in which Google-owned VirusTotal will play an important role.
While it is unclear at the moment what exactly Chronicle will do, the use of VirusTotal's data is certainly interesting, given how important it is as a resource both for individual researchers and for security companies.
Despite the popularity of the service, there are many persistent myths about VirusTotal. In a paper presented at VB2017 in Madrid, security researcher Randy Abrams provided an introduction to the service and then busted many of these myths. (Randy presented the paper as an independent researcher, but has since joined Webroot as a senior security analyst.)
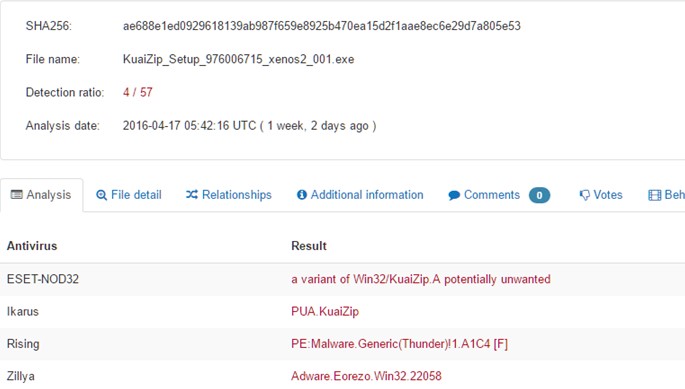
Results of running a sample through VirusTotal.
You can read Randy's paper 'VirusTotal tips, tricks and myths' in both HTML and PDF format. We have also uploaded the video of his presentation to our YouTube channel.