Posted by Martijn Grooten on Feb 1, 2018
In late spring of 2011, a sudden rise in the price of Bitcoin – reaching almost US$30, up from less than $1 barely a month earlier – attracted the attention of malware authors. They added mining capabilities to their malicious creations and made them look for Bitcoin wallets, while many websites added JavaScript code that used visitors' CPUs to mine for Bitcoin.
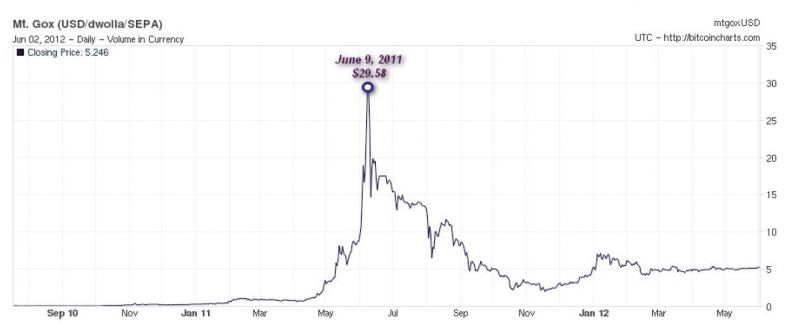 Fluctuating value of BTC in $USD.
Fluctuating value of BTC in $USD.
The situation is surprisingly similar six and a half years on, as the meteoric rise in value of many cryptocurrencies in late 2017 has once again attracted the attention of malware authors. Though for mining purposes other cryptocurrencies (most notably Monero) are more efficient, many of today's malware campaigns deliver miners, and many compromised websites have visitors' devices engage in in-browser mining.
A report published this week by Cisco Talos looked at how extremely profitable such activities can be.
One of the earliest papers that looked at malware families targeting Bitcoin was presented at VB2012 by Microsoft researcher Amir Fouda. For this week's Throwback Thursday, we publish Amir's paper in both HTML and PDF format.
