Posted by Martijn Grooten on Mar 19, 2018
Last Wednesday, Belgium-based Polish hacker Thomasz T. was arrested during a visit to his home country. Thomasz is believed to be the author of the Polski, Vortex, and Flotera ransomware families.
Though this may look impressive on one's cybercrime CV, it turns out that Thomasz may not be the most skilled of hackers. At VB2017 in Madrid, Polish security researcher and journalist Adam Haertlé presented a paper about him, the title of which is quite telling: "The life story of an IPT - Inept Persistent Threat actor".
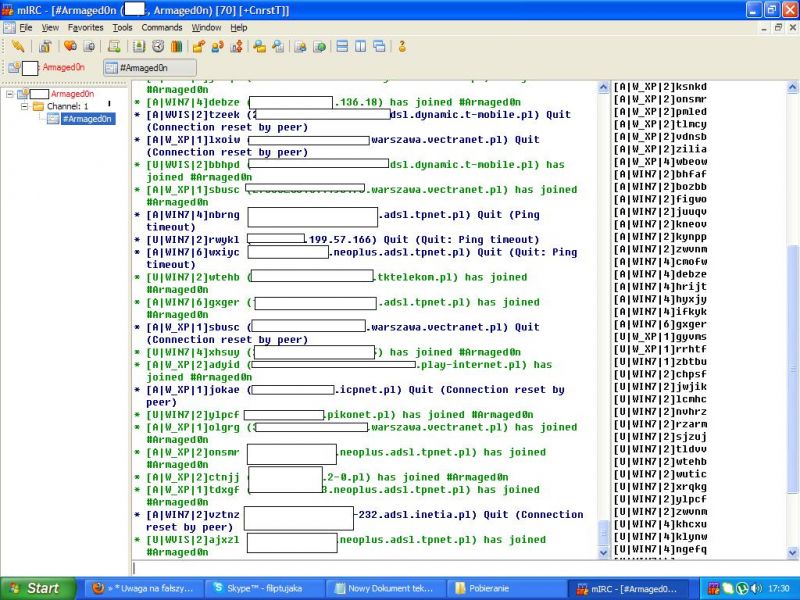
Botnet C&C traffic.
Following Thomasz's arrest, we have published Adam's paper on our website in both HTML and PDF format, and we have uploaded the video of his presentation to our YouTube channel. We have also published Adam's slides (pdf), for anyone who wants to look at Thomasz's online adventures in a bit more detail.