Posted by Martijn Grooten on Mar 7, 2018
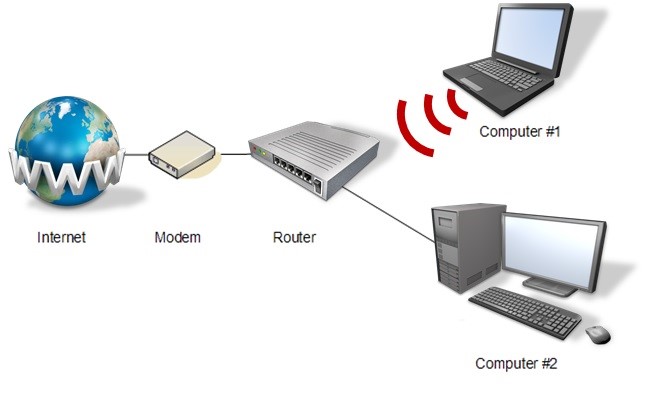
In recent years, we have seem a significant increase in malware targeting routers. Given that, unlike most endpoint devices, routers are often connected directly to the internet, and given that many of them have known vulnerabilities, it is easy to see why they are so attractive to cybercriminals.
At VB2017 in Madrid last year, Symantec researcher Himanshu Anand presented a paper (co-written with his colleague Chastine Menrige) on router malware, in which he both gave an overview of the topic and looked at some individual case studies.
You can read the paper 'The router of all evil: more than just default passwords and silly scripts' in both HTML and PDF format.
We have also uploaded the video of Himanshu's presentation to our YouTube channel.
Have you analysed a new online threat? Do you know a new way to defend against such threats? Are you tasked with securing systems and fending off attacks? Don't forget that the call for papers for VB2018 (Montreal, 3-5 October) is currently open and we want to hear from you! The deadline for submissions - 18 March - is fast approaching, so make your submissions now!