Posted by Martijn Grooten on Apr 25, 2018
If the Internet is, as is often said, held together with elastic bands and pieces of Sellotape, BGP is essentially a bunch of post-it notes that serve as traffic signs.
BGP hijacks – in which a malicious attacker essentially takes over one or more ranges of IP addresses – are not extremely common, but for a protocol that is so essential to the Internet's functioning, they occur worryingly often. In 2014, a BGP hijack resulted in $83k of freshly mined Bitcoins being stolen. In a VB2016 conference presentation, Mike Benjamin of Level 3 Communications talked about the various issues that exist with the protocol.
Yesterday, a BGP hijack resulted in five IP ranges that belonged to Amazon's infrastructure being 'stolen' for about two hours and being routed to a network controlled by attackers. This gave the attackers control of Amazon's DNS responses, which they used in order to point the DNS of MyEtherWallet, a web-based wallet for the Ether cryptocurrency, to a server hosted in Russia.
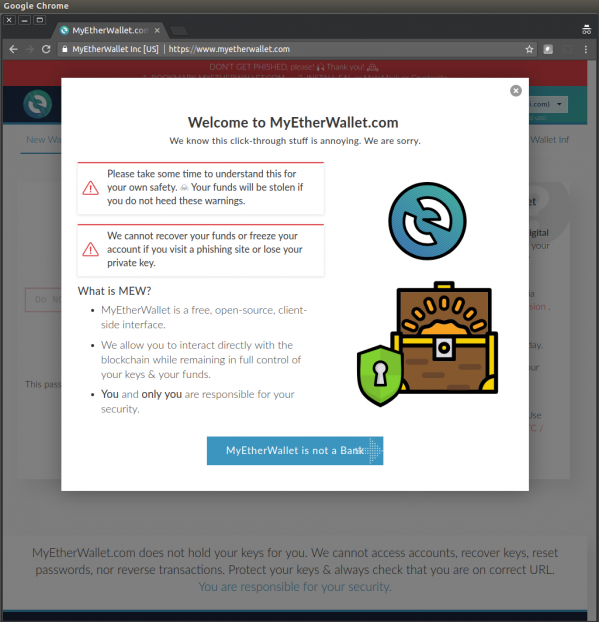
DNS hijacks aren't a new phenomenon; in December, security firm Fox-IT published details of how a DNS hijack had been used against its systems. In that instance, the attackers used the control they had gained over DNS to generate a valid certificate for the domain. Those targeting MyEtherWallet didn't bother with that, nevertheless it appears that several people clicked through the certificate warning to visit a phishing version of MyEtherWallet's website, resulting in some $150k worth of digital currency being stolen.
The issues with BGP and DNS are an Internet-wide problem that can't be solved by an individual website or service, but there are some ways to mitigate the risks, which for high-risk services are worth considering.
The general usefulness of DNSSEC, which checks the digital signature of DNS responses, is debatable, but in this case it could have prevented the DNS takeover through a BGP hijack. HTTP Strict Transport Security (HSTS), which forces a previously seen connection always to use HTTPS, would have prevented the end-user from being able to ignore the certificate warning.
Maybe none of this really matters, though. There has been some speculation that the MyEtherWallet phishing could have been a smokescreen for another, more advanced attack. A number of people have pointed out that it is quite odd that the wallet to which the stolen funds were transferred already contained $17m worth of cryptocurrency.