Posted by Martijn Grooten on Apr 19, 2018
Ever since their return more than four years ago, initially in targeted attacks and later in large-scale malware campaigns, Office macros have been one of the most prominent ways to spread malware.
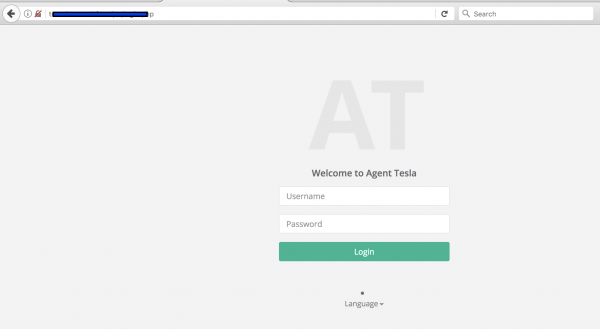
Today, we publish a research paper by Aditya K. Sood and Rohit Bansal of SecNiche Security, in which they analyse a malware campaign in which VBA macros are used to execute PowerShell code, which in turn downloads the actual payload: the Tesla information-stealing trojan.