Posted by Martijn Grooten on May 30, 2018
Researchers at IBM X-Force have discovered a new banking trojan, dubbed 'MnuBot', which is targeting Internet users in Brazil.
The trojan performs tasks common to banking malware, such as logging keystrokes, creating screenshots and overlaying the bank's website with an invisible form. What is most noticeable, though, is the use of a Microsoft SQL server for C&C communication.
It is common for malware authors to put a lot of effort into trying to evade detection both of the activities on the endpoint and of all network communication. The use of SQL server could just be another example of that. However, I agree with SANS's Johannes Ullrich who, speaking on his daily podcast, pointed out that simply using HTTPS would have sufficed to make the network traffic undetectable.
Moreover, the credentials required to access the SQL database are present in the malware itself: they are dynamically decrypted just before the connection to the database server is made, making them accessible to someone analysing the malware.
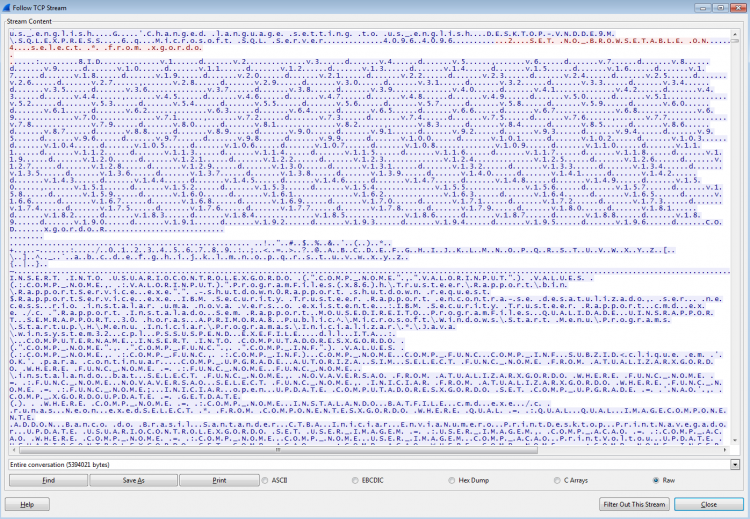
MnuBot's network communication in Wireshark clearly shows the SQL commands used. Source: IBM.
Brazil has long been a hotbed of cybercrime and there are many malware families that specifically target the country's Internet users. As IBM's Jonathan Lusky said in the blog post about the malware, the use of overlaying forms and the creation of new desktops are techniques seen in other Brazilian banking malware too.
Update: shortly after this blog post was published, Kaspersky Lab researcher Fabio Assolini, who has regularly spoken at VB conferences on cybercrime in his native Brazil, contacted us to say that he has seen this technique being used since 2014 and pointed out a 2015 McAfee blog post which describes an example of a similar technique.