Posted by Martijn Grooten on May 22, 2018
A current trend sees DDoS attacks focusing less on large volume attacks and more on attacks that exhaust server resources, Cloudflare reports.
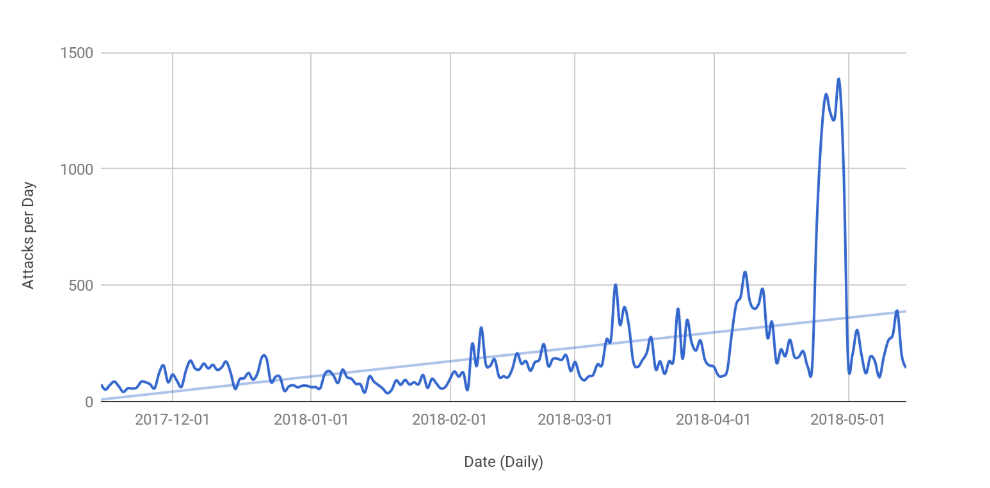 The number of layer 7 attacks per day. Source: Cloudflare.
The number of layer 7 attacks per day. Source: Cloudflare.
This makes sense. The purpose of a DDoS attack is to render a service unavailable, and as increased defences have made it harder to do so simply by sending a large volume of data to the server, attackers have switched their focus to sending requests that exhaust server resources (such as CPU, memory and disk).
A typical example would be sending HTTP requests that result in complicated search queries on the web server's database. A poorly protected server can become unavailable if it has to handle too many such requests.
A similar evolution has been seen in other kinds of attacks, such as botnets and spam: first they went through a phase in which volume was the determining factor, which was then followed by a phase in which attacks were on a smaller scale and incorporated relatively more sophistication.
This evolution from 'quantity' to 'quality' is often a response to improved defences, but it is worth noting that defences often get better because large-scale attacks are relatively easy to detect – meaning that less volumetric attacks are not necessarily a good thing.
Thus, while it may be tempting to measure the severity of an attack by the number of emails sent, the number of infected machines, or the number of GB transferred per second, in many cases these are not what makes an attack serious.