Posted by Martijn Grooten on Jun 13, 2018
As modern browsers have become harder to attack, malware authors have found a simple way around this: by working with the browser rather than against it. More particularly, by tricking users into installing extensions they host on official browser stores, like the Google Chrome Store.
Malicious Chrome extensions have been used for various nefarious activities, from banking fraud to delivering backdoors and stealing cryptocurrencies. Google, of course, works hard to detect and block such extensions, but as is so often the case in security, it is never 100 per cent successful.
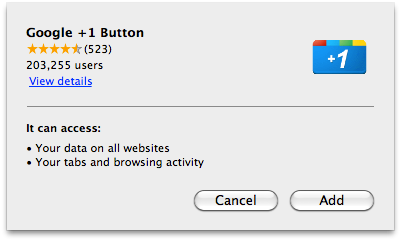
The company has now, however, made a subtle change that should make it easier for users to detect when they are installing an extension. Until now, it has been possible for websites to offer inline installation of an extension, where a pop-up appears asking the user whether they want to install the extension. Users often read such pop-ups as if they are saying "click 'OK' to continue browsing this website", and thus unwittingly agree to the installation of extensions offered by compromised or malicious sites.
Google has now banned inline installation for new extensions and later this year will disable inline installation altogether. Instead, a site that wants to offer an extension will have to send users to the Chrome Store. Of course, this won't stop gullible users form being tricked into installing malicious code, but malware authors will have to work a bit harder on social engineering.
The fight against malware is rarely about being able to stop things altogether, but about making small steps that can sometimes lead to a large reduction in the number of infections. Justin Schuh, from Google Chrome's security team, promises more changes to combat malicious browser extensions.
Yeah, that's the gist. This closes the lowest friction vector for social engineering, which helps with all manner of unwanted software. And like I noted in my tweet, there's more changes in the works to combat these things.
— Justin Schuh (@justinschuh) 12 June 2018