Posted by Martijn Grooten on Jul 10, 2018
A malware campaign has been using code-signing certificates stolen from Taiwanese companies to sign its samples, ESET researcher and regular VB conference speaker Anton Cherepanov writes.
Malware signed with stolen certificates isn't a new phenomenon. Stuxnet famously used stolen certificates, also from Taiwanese companies, and in 2016 Symantec wrote about a malware campaign that used no fewer than nine stolen certificates. A year earlier, IBM's Limor Kessem looked at the phenomenon of code signing being offered as a service in the cybercrime underground.
In this particular case, two malware families were using the stolen certificates: the PLEAD backdoor (analysed by JPCERT/CC last month) and a password stealer that steals passwords from various browsers. Both malware families are linked to the BlackTech cyber espionage group that Trend Micro wrote about last year and whose activities focus particularly on Taiwan.
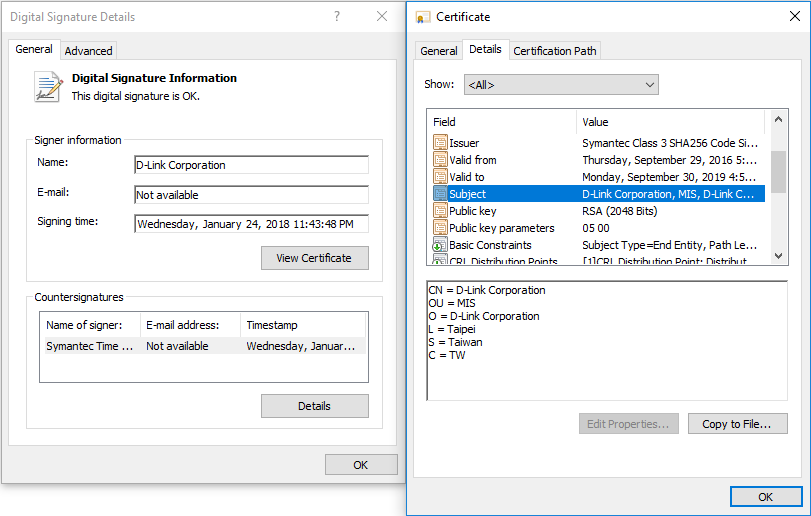 D-Link was one of the companies whose certificates was stolen. Source: ESET.
D-Link was one of the companies whose certificates was stolen. Source: ESET.
In his blog post, Cherepanov lists a number of indicators of compromise, including the serial numbers of the two affected certificates, both of which have now been revoked. This shows another, more positive side to the use of stolen certificates by malware authors: once the certificate theft has been discovered, it does help defenders find the malware more easily.
Something similar occurs with DKIM, which is used to sign emails and which plays an important role in the fight against unwanted and malicious emails. DKIM private keys can also be stolen, but doing so won't give an adversary more than a short-term advantage: once the malicious use of a DKIM key is discovered, which in the case of email often happens quickly and automatically, emails that are signed with with are actually more likely to be blocked.