Posted by Martijn Grooten on Aug 14, 2018
AhnLab has published a research paper that looks at the Red Eyes group, which is particularly active against North Korean defectors, as well as journalists and human rights activists in the North Korean community. The paper (pdf) is written by Minseok (Jacky) Cha and was originally published in Korean in April of this year.
Red Eyes is known by various names: in a research paper published in February, FireEye called it APT 37, while Cisco Talos, who first discovered the group in March of last year, refers to it as Group 123. The group was also mentioned in a paper presented by Talos researchers Paul Rascagneres and Warren Mercer at VB2017 last year.
Paul and Warren showed an example of what, according to Minseok, is the most common way this group infects its targets: by sending a malicious Hangul word processing file, often exploiting a vulnerability in the handling of EPS objects. However, the group has also exploited the DDE feature, as well as a then zero-day vulnerability in Adobe Flash Player.
The Red Eyes group has been active since at least September 2016, but its activities have been linked to another attack group, active from at least July 2015. Minseok also points out that strings used in the group's malware suggests its authors are native speakers of Korean and that they sometimes use a version of the language that sounds more natural to those living in the northern part of the Korean peninsula.
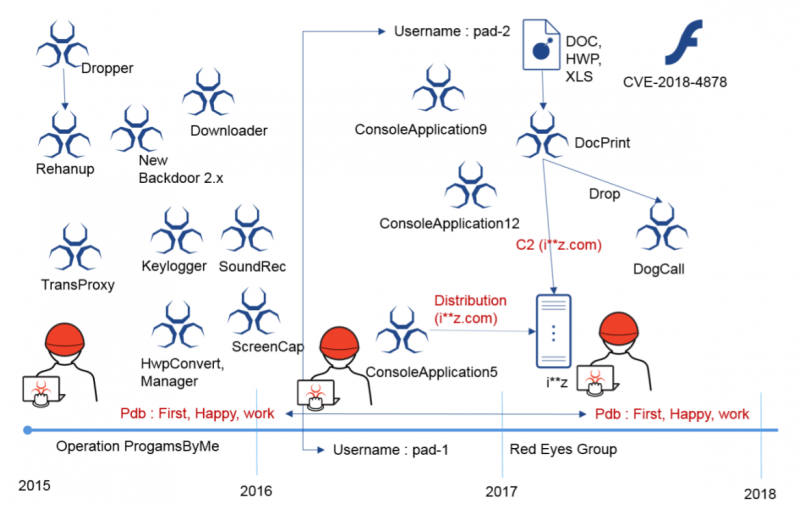 Activities of the Red Eyes group and the likely linked ProgamsByMe [sic] group.
Activities of the Red Eyes group and the likely linked ProgamsByMe [sic] group.
Cyber attacks and threats linked to North Korea will be a hot topic at VB2018, with several papers papers dealing explicitly or implicitly with threats that have been attributed to North Korean actors. Minseok himself will present a paper on lesser-known activities by the Lazarus Group. For those interested in the subject, I also recommend reading the blog posts recently published by Intezer and McAfee that look into code reuse among various groups linked to North Korea.
Registration for VB2018 is open now, and for hot security research, the call for last-minute papers also remains open until 2 September.
Make sure to join us in Montreal to learn about and discuss the most important threats facing the Internet today!