Posted by Martijn Grooten on Oct 30, 2018
It may be hard to believe, but it was only eight months ago that the 2018 PyeongChang Winter Olympic Games were targeted by malware named Olympic Destroyer. Though not the first time the Olympic Games had been the target of malware, Olympic Destroyer, as its name suggests, did appear to be destructive in nature.
Cisco Talos researchers Paul Rascagnères and Warren Mercer were among the first to write about the malware. They also presented a detailed paper about it at VB2018 in Montreal.
In their paper, as well as in their presentation in Montreal, they analysed the malware and looked at one particular issue that made Olympic Destroyer noteworthy: attribution. The malware appeared to contain various false flags that could (and in some cases did) confuse attribution. The authors warn that attribution isn't as easy as it often seems.
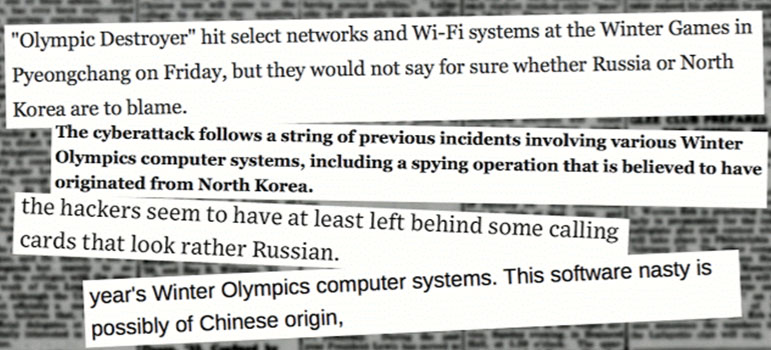 Different media outlets published conflicting stories in relation to attribution.
Different media outlets published conflicting stories in relation to attribution.
We have now published Paul and Warren's paper in both HTML and PDF format. We have also uploaded the video of their presentation to our YouTube channel.