Posted by Martijn Grooten on Nov 29, 2018
Yesterday, a federal grand jury in the US unsealed an indictment charging two Iranians with being behind the SamSam ransomware.
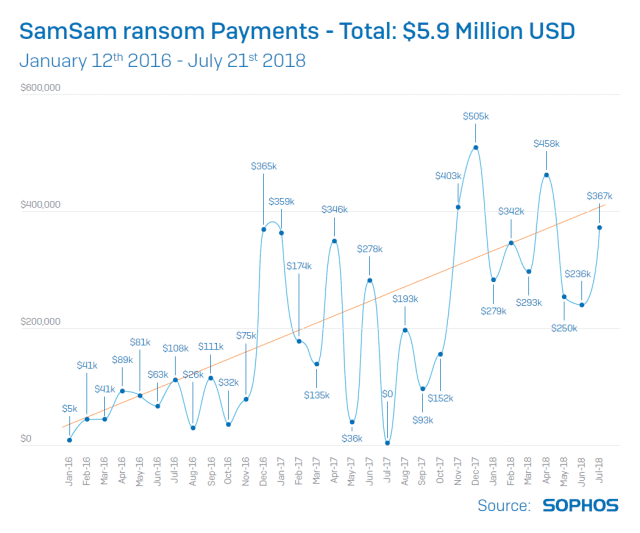
SamSam has been one of the most successful ransomware campaigns in recent years, thanks to the clever targeting of specific organisations, including universities, hospitals and local governments. This targeting allowed the attackers to ensure the targeted organisation really couldn't recover the files without the private key, enabled them to create a very smooth 'support' process for those victims that did pay, and to make large very ransom demands: the group is believed to have received more than US$6m in ransom payments, with the number of losses through damages believed to be five times as high.
The best source on the ransomware is a Sophos paper from this summer. This report was also the source of a presentation Sophos researcher Andrew Brandt gave on the ransomware at VB2018, in which he described the history and the inner workings of the malware, as well as how the actors behind it had remained hidden for so long.
It is unclear whether in the current political climate (and given the fact they do not appear to have targeted Iranian organisations) the alleged SamSam authors will face justice, or even whether their indictment will bring an end to their activities. But it does serve as a reminder that even attackers with good OPSEC, such as those behind SamSam, have a very hard time staying hidden.
We have uploaded Andrew's VB2018 presentation to our YouTube channel.