Posted by Martijn Grooten on Nov 16, 2018
"Capable, well-resourced, and they go back decades." The Turla threat group doesn't make the news as much as some other Russian-speaking APT groups, but it is one of the most advanced and most diverse groups out there.
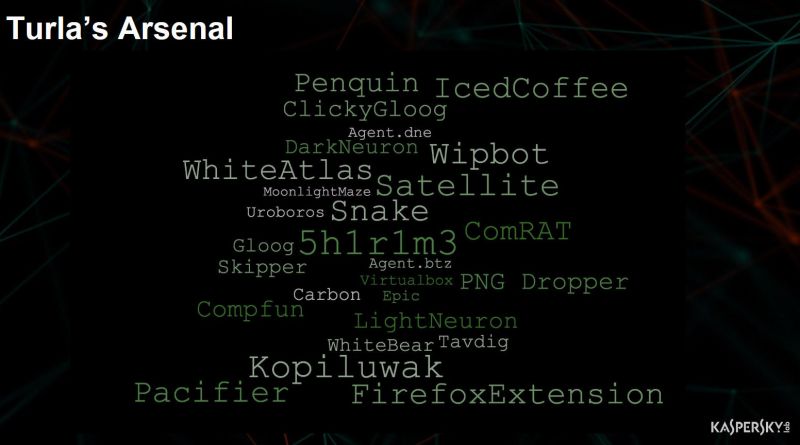
At VB2018 in Montreal, Kurt Baumgartner and Mike Scott from Kaspersky Lab's GReAT detailed the latest malware and infrastructure seen used by Turla, including some open-source tooling, which is rather surprising for a group with such advanced development skills.
You can watch the video of Kurt and Mike's presentation on our YouTube channel. For more on Turla, you can also watch the presentation Kurt gave three years ago at VB2015 in Prague, which focused on its use of satellite networks for C&C communication, or read a paper F-Secure's Mike Low wrote for Virus Bulletin in 2014.
Turla will also be covered in a lightning talk Kurt will give at the first CYBERWARCON conference, which takes place on 28 November in Arlington, Virginia, USA. Tickets for this conference are still available.