Posted by Martijn Grooten on Nov 13, 2018
From NotPetya to Shadowpad, supply chain attacks have become a serious and hard-to-fight security problem. One prominent type of supply chain attack involves the pre-installation of malware on (often) cheap Android devices.
At VB2018 in Montreal, Google researcher Łukasz Siewierski talked about one such case: that of the multi-purpose 'Triada' trojan. First discovered by Kaspersky Lab in 2016 and further analysed by Dr. Web a year later, Triada found itself pre-installed on many devices through various OEMs.
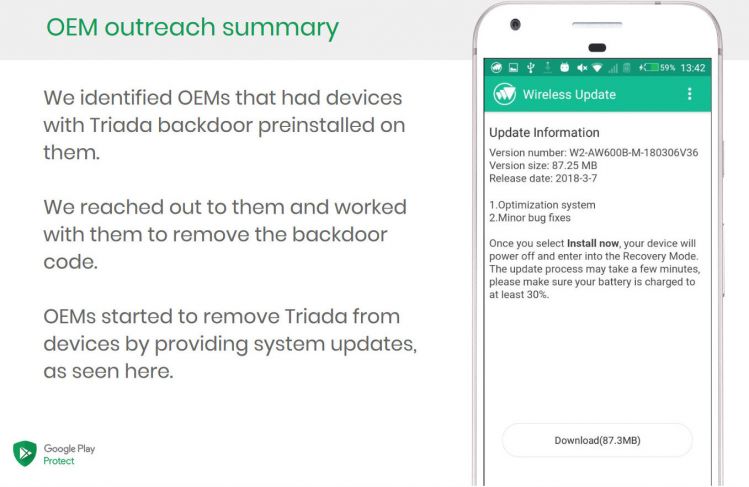
In his presentation, Łukasz looked at Triada's technical properties and at the evolution of the malware, before going on to describe a successful operation between Google and the OEMS that led to the removal of the malware from infected devices.
We have uploaded the video of Łukasz's VB2018 presentation to our YouTube channel. Next month, he will be speaking on the same subject at Botconf in France.