Posted by Martijn Grooten on Mar 8, 2019
OSX/Pirrit was first analysed in 2016 by Cybereason's Amit Serper in a guest blog post for the Objective See blog. It is an interesting and technically thorough analysis of a piece of adware that, as is not uncommon, uses techniques borrowed from malware.
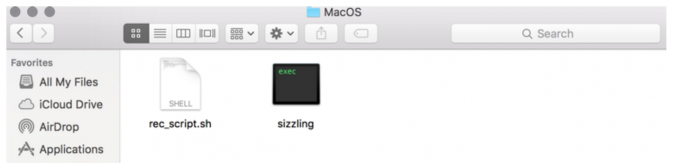 Pirrit appears as an unsigned executable inside an app bundle, source: Objective See.
Pirrit appears as an unsigned executable inside an app bundle, source: Objective See.
What happened next is also not entirely unheard of: Cybereason and Amit himself both started receiving legal threats from the company behind the adware. This led to a follow-up report (pdf) in which not only was the adware analysed but the legal threats were also discussed and Cybereason outlined its reasons for referring to the software as 'malware'. The use of an OS X zero-day exploit certainly contributed to that.
At VB2018 in Montreal, Amit gave a presentation in which he discussed both the adware and the legal threats he and Cybereason received. We have now uploaded the video of Amit's presentation to our YouTube channel. It is well worth watching right to end, including the message he has for fellow malware researchers who may find themselves in a similar situation.
Don't forget you have until the end of next week (deadline 17 March) to submit a paper for VB2019, the upcoming Virus Bulletin conference, which takes place 2-4 October in London, UK.