Posted by Martijn Grooten on Jun 4, 2019
The Lazarus Group, generally linked to the North Korean government, is one of the most notorious threat groups of recent years. It has engaged in digital espionage, destructive attacks and financially motivated attacks, and was probably the most discussed threat group at VB2018 in Montreal.
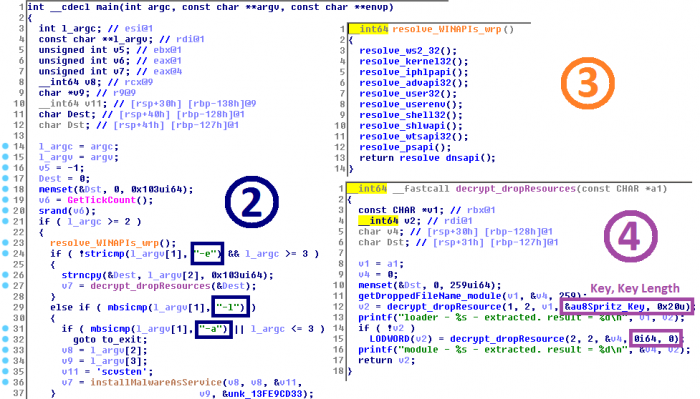
One of the Lazarus-related papers at VB2018 was written by ESET researchers Peter Kálnai and Michal Poslušný and presented by the former in Montreal. In their paper, the researchers looked at various campaigns linked to Lazarus (including some that had not previously been published) and at what links them.
The authors presented the same research at CONfidence in Kraków yesterday. Today, we have published Peter and Michal's paper - you can read it in both HTML and PDF format. We have also uploaded the recording of Peter's VB2018 presentation to our YouTube channel.
 Lazarus Group: a mahjong game played with different sets of tiles
Lazarus Group: a mahjong game played with different sets of tiles
At VB2019 in London, Peter and Michal will be back to present a paper on Rich Headers seen in PE files.
Registration for VB2019 is now open; early bird rates apply until 30 June.