Posted by Martijn Grooten on Aug 5, 2019
The number of active exploit kits is very small: the recently published summer 2019 edition of Malwarebytes' quarterly round-up lists the seven then known active exploit kits. To that, a potential eighth has now been added, thanks to Virus Bulletin researcher Adrian Luca.
During his work on the VBWeb tests for web security products, Adrian spotted a new kit that calls itself 'Lord EK', although at the time the kit was still in development.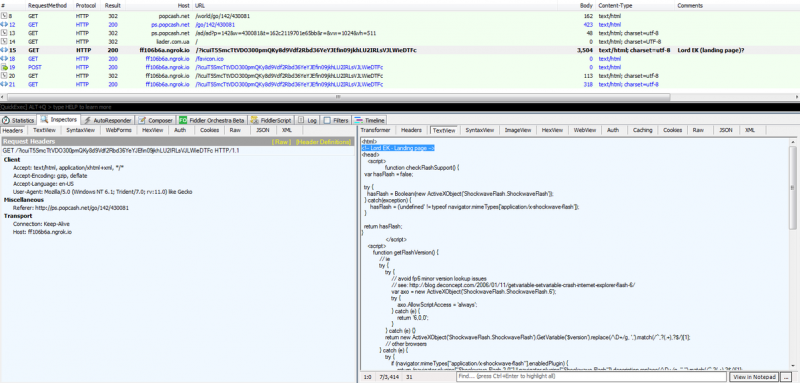
The Lord exploit kit has since been analysed by Brad Duncan, on his Malware Traffic Analysis website, and by Jérôme Segura at Malwarebytes. Jérôme notes how it checks for the Flash Player version in an attempt to exploit CVE-2018-15982, a vulnerability popular in exploit kits today.
Jérôme notes that, interestingly, the threat actor uses the 'ngrok' service, which creates a secure tunnel from the Internet to a local server. The fact that ngrok also creates random subdomains makes it ideal for the exploit kit author. It is the first known use of ngrok by exploit kits, though it was used by the Lokibot malware in a campaign this spring.
We will keep a close eye on further developments of this exploit kit. In the meantime, if you would like the VB team to test your web security product's detection of exploit kits and other web-based threats tested, please contact us.