Posted by Martijn Grooten on Sep 18, 2019
Following the resumption of activity by Emotet's C&C servers in August, it was only a matter of time before the botnet started sending out spam again. This did indeed happen on Monday morning.
Many, though not all, of the emails Emotet sent out this week used a trick that the malware has used before: sending the malicious spam as apparent replies to previously harvested emails.
This has a number of advantages for the spammers. First, it makes the emails seem credible. Not only do they appear to come from known contacts, they also tend to contain messages such as "find the new document attached" that would seem an appropriate reply to many emails.
Secondly, because most of the email body contains the quoted email that is being replied to, content filters are less likely to block it.
And thirdly, by sending these emails as replies to harvested emails, they are likely to evade most spam traps. Spam campaigns hitting a large number of spam traps is probably the factor that contributes most to the emails in the campaign getting blocked; this is why most of today's malicious spam campaigns are sent in much smaller volumes.
Emotet's recent campaign didn't manage to evade spam traps entirely though, because some of the harvested emails were spam themselves; possibly with forged senders. Some of the emails we saw in our tests were such replies which, amusingly, included emails with an 'updated document' in response to dating spam.
Even so, we noted that many products in our test lab failed to recognise the emails as either spam or malicious. This is part of a worrying trend we have seen for a while, with malicious spam campaigns having much higher delivery rates than regular spam, sometimes as much as ten per cent of the emails piercing through the first defence layer.
Apart from 'hijacking' email threads, Emotet also avoids detection by sending most of its spam campaigns through compromised but legitimate mail servers. Such servers aren't likely to be listed on IP blocklists; IP-based defences are a very effective first defence layer in any email security product.
Spam is often seen as a problem of volume, but this has long since ceased to be the case: Emotet and other malware spreading via email campaigns is sent out in relatively low-volume campaigns, resulting in relatively high delivery rates and likely better returns on investment.
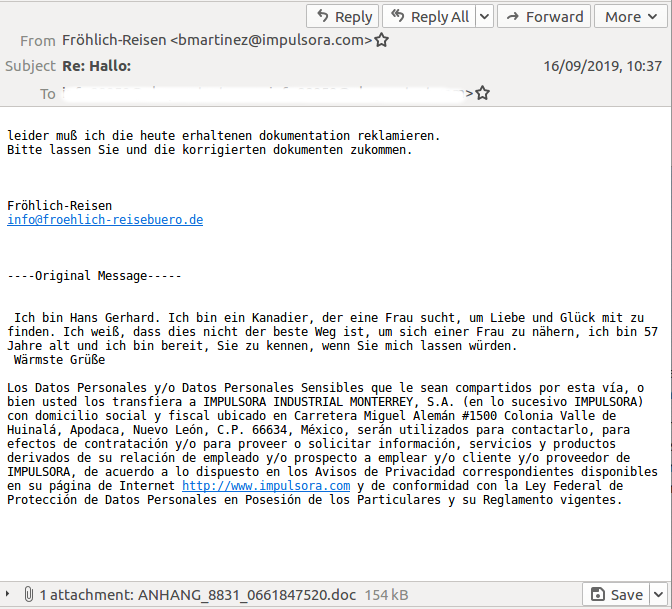
No fewer than nine email security products missed this Emotet campaign, despite it being a reply to a dating spam email.
Malwarebytes performed a technical analysis of the most recent campaigns, in which obfuscated macros in the attached Office files downloaded the Emotet binary from compromised WordPress sites.
At VB2019 in London next month, Sophos researcher Luca Nagy will present a paper on Emotet, while ZEROSPAM researchers Pierre-Luc Vaudry and Olivier Coutu will present a last minute paper on tackling the conversation thread hijacking Emotet is doing.
You can still register to see these and 50 other presentations on all aspects of threat intelligence. VB2019 takes place 2-4 October at the Novotel London West hotel in London, UK.