Posted by Martijn Grooten on Oct 28, 2019
Magecart is an umbrella-term for various groups that engage in placing JavaScript code on e-commerce sites to steal credit card info. Magecart attacks go back almost a decade but it became an infosec household name following some prominent breaches in 2018.
Magecart is getting a lot of attention from security researchers, and RiskIQ's Yonathan Klijnsma is probably the most prolific among them. He was one of the authors of a 2018 report that detailed the modi operandi of the various Magecart groups.
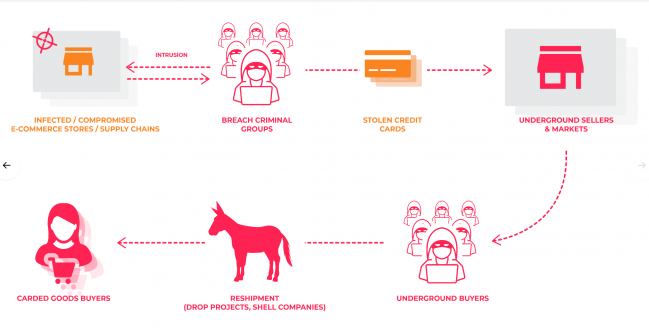 A rich underground economy exists around all the different steps needed to monetize a breach.
A rich underground economy exists around all the different steps needed to monetize a breach.
At VB2019 in London earlier this month, Yonathan also presented a paper on Magecart in which he looked at some of the more interesting groups and the latest Magecart trends.
Today we publish Yonathan's paper in both HTML and PDF format. We have also uploaded the video of his VB2019 presentation to our YouTube channel.
