Posted by Martijn Grooten on Nov 4, 2019
Emails with a malicious link or attachment form only a small minority of the spam that is sent every day. If it appears that such emails are more common than that, it is not just because such emails are potentially more damaging: we have repeatedly seen that they are far more likely to bypass email security products than ordinary spam.
This was no different in October, when we saw many emails bypass more than a third of the products in our test lab. Looking at the emails that were most often missed, one thing stood out: almost all of them delivered Emotet.
The notorious trojan, which came back from a summer hiatus in September, is best known for its ability to evade detection and as the stepping stone for some very damaging attacks. But Emotet's operators are also known to be very effective spammers.
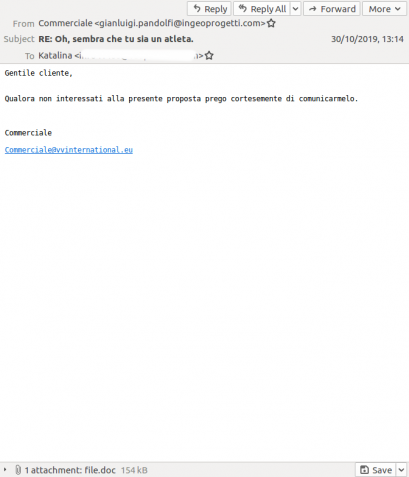
In some campaigns they send emails as replies to previously sent legitimate emails, but in the last month the emails we saw simply used short, generic messages that would be hard to distinguish from legitimate emails. Crucially, they used compromised mail servers from which to send the emails, which in most cases allowed them to pass SPF and DKIM.
Another thing that contributes to the relatively low block rate of this and other malicious campaigns is the small size of the campaign: sending millions of copies of the same email hurts spammers more than it helps. In fact, Emotet's campaigns tend to be relatively large compared with others – some malware is sent in campaigns of as few as 25,000 emails. It is likely that some of the campaigns sent in October did not make it to our test lab but would have achieved even lower block rates.
This doesn't mean that every malicious spam campaign achieves low block rates: also in October we noticed a malware campaign targeting users in Italy spreading Ursnif. The emails were sent from compromised Italian home IP addresses and were not only blocked by every email security product in our test but also by almost all IP- and domain blocklists.
 |
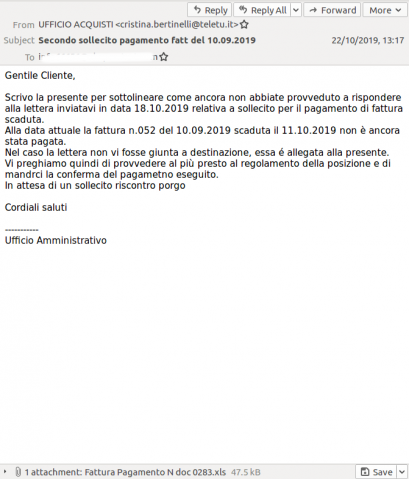 |
Two malicious emails in Italian: Emotet (left) bypassed more than a third of email security products, while Ursnif (right) was blocked by all products.
For more details on Emotet, I recommend you consult the VB2019 paper by Sophos researcher Luca Nagy.
I will speak on the subject of malicious spam at Botconf in Bordeaux, France next month. Should you wish to have your email security product added to our test lab (and, optionally, have it certified by Virus Bulletin), please email [email protected].