Posted by Martijn Grooten on Dec 27, 2019
Over the years, many ‘potentially unwanted applications’ have plagued macOS in the same way they have plagued other platforms. Though anti-virus isn’t ubiquitous on Macs, detecting such PUAs usually isn’t a difficult problem.
However, there are exceptions. One such exception is a popular yet unnamed piece of ‘bundleware’ that was analysed by Sophos researcher Sergei Shevchenko in a paper presented at VB2019 in London. The bundleware performs many obfuscation and anti-analysis techniques that are typical of malware and is used to download other software on systems on which it is installed.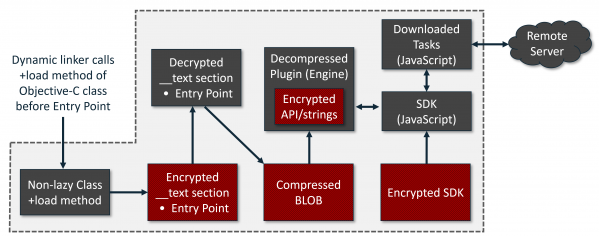
Today we publish Sergei's paper in both HTML and PDF format. We have also uploaded the recording of his presentation at VB2019 in London to our YouTube channel.
 Never before had Stierlitz been so close to failure (or: what is a Soviet super-spy doing in a popular bundleware for Mac?)
Never before had Stierlitz been so close to failure (or: what is a Soviet super-spy doing in a popular bundleware for Mac?)