Posted by Helen Martin on Dec 3, 2019
Different forms of malware and cyber threats are constantly making the news headlines, and one could be forgiven for thinking that threats like ransomware, fileless malware, rootkits and phishing are all new phenomena. But are they really? This is the question asked – and answered – by industry veterans Righard Zwienenberg (ESET) and Eddy Willems (G DATA) in their paper and presentation at VB2019 in London.
Eddy and Righard's entertaining presentation looked at the relationship between current threats and past threats, and revealed that there are more commonalities than we might at first think. "New" types of threat are not so new after all – we simply keep making the same mistakes.
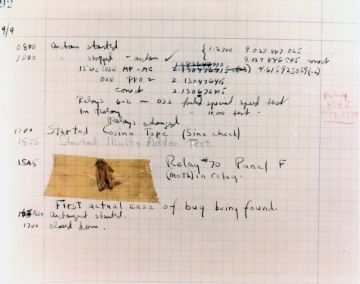 In 1947 Grace Hopper, one of the first computer programmers, described the first computer 'bug' in her logbook (source: Naval History and Heritage Command).
In 1947 Grace Hopper, one of the first computer programmers, described the first computer 'bug' in her logbook (source: Naval History and Heritage Command).
Today we publish Righard and Eddy's paper in both HTML and PDF format. We have also uploaded the video of their VB2019 presentation to our YouTube channel.