Posted by Martijn Grooten on Dec 10, 2019
Latin America has long been a hotbed for cybercrime, but the region has also seen the activity of various APT groups. One of these groups makes use of 'Machete', a Python-based toolset.
Machete dates back at least nine years and was first written about by Kaspersky in 2014. In August of this year, ESET published a paper on the group's recent targeting of Venezuelan government institutions.
For VB2019 in London, Veronica Valeros, Maria Rigaki, Kamila Babayeva and Sebastian García, researchers from the Stratosphere Lab at the Czech Technical University in Prague, co-wrote a paper on Machete. The paper contains a very in-depth analysis of the tool, looking at the full timespan during which it was developed.
The researchers noted the ability to exfiltrate data through USB devices, suggesting some of the actors using it may have had physical access to the targeted systems. They also looked at decoy documents used by the actors, which gives some insight into the targets.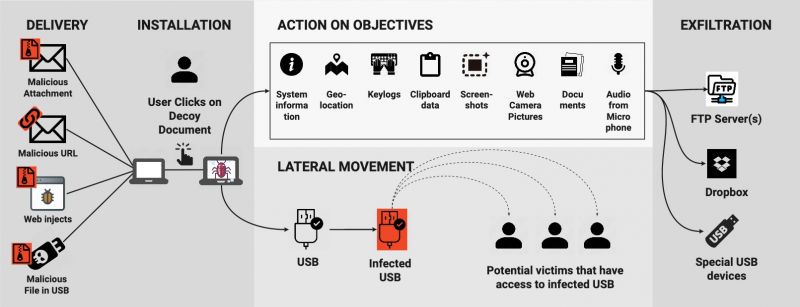 Machete operations are structured in five phases: delivery, installation, action on objectives, lateral movement and exfiltration.
Machete operations are structured in five phases: delivery, installation, action on objectives, lateral movement and exfiltration.
Today, we have published the researchers' paper in both HTML and PDF format. We have also uploaded the video of the presentation, delivered by Veronica and Maria in London, to our YouTube channel.
 A study of Machete cyber espionage operations in Latin America
A study of Machete cyber espionage operations in Latin America