Posted by Helen Martin on Jan 28, 2020
It is estimated that between 8% and 9% of the population worldwide suffers with some form of diabetes.
People with type 1 diabetes typically have to measure their blood glucose levels several times a day and adjust their treatment according to the results. Traditionally, this has been done by means of the person pricking their finger to draw a drop of blood, from which the levels of glucose are measured. A relatively recent innovation that can help make this process less arduous – and less intrusive – is an IoT device that automatically measures the levels of glucose in a person's blood without the need for them to prick their finger.
Clearly a welcome innovation for those affected by the disease, but are there any security risks?
In a paper written for VB2019, Fortinet researchers Axelle Apvrille and Aamir Lakhani asked: what threats are faced by diabetes sufferers who want to use medical IoT devices?
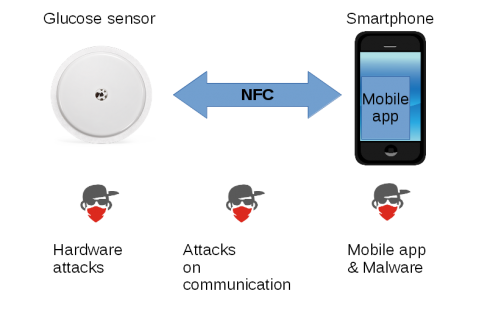
Privacy and security threats on a Flash Glucose Monitoring system.
The researchers looked at potential threats from three different angles: the security and privacy the IoT devices themselves, the existence of diabetic-related pieces of malware, and the trading in patient records on the Darknet.
Today we publish the researchers' paper in both HTML and PDF format, as well as the recording of the presentation given by Axelle in London.
Have you carried out research that furthers our understanding of the threat landscape? The Call for Papers for VB2020 in Dublin is open! Submit your abstract before 15 March for a chance to make it onto the programme of one of the most international threat intelligence conferences.