Posted by on Mar 12, 2020
Malicious RTF files, exploiting vulnerabilities in Microsoft Office, have long been a popular way to deliver malware, most often through (spear-)phishing attacks. Such files are often created using exploit builders, which were the subject of a VB2018 presentation by Sophos researcher Gábor Szappanos.
One such builder (or weaponizer) is ‘Royal Road’, which has been used by various Chinese APT groups to deliver malware. Royal Road and how the properties of RTF files can be used to track weaponizers and their users were the subject of a VB2019 paper by Michael Raggi (Proofpoint) and Ghareeb Saad (Anomali).
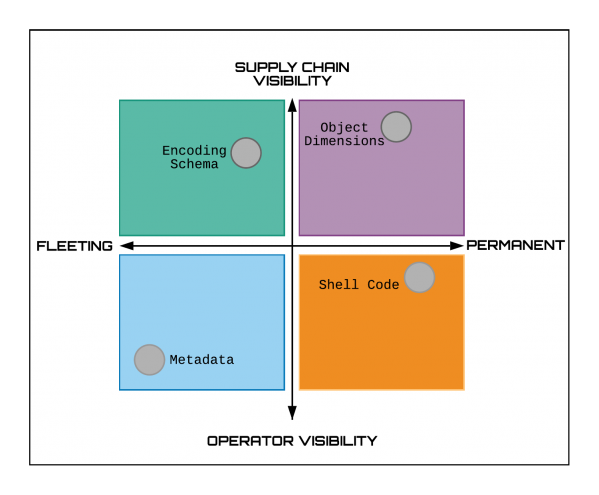 Permanence versus operational visibility in RTF attribution techniques.
Permanence versus operational visibility in RTF attribution techniques.
Today, we publish the researchers' paper in both HTML and PDF format as well as the recording of their VB2019 presentation.
 Attribution is in the object: using RTF object dimensions to track APT phishing weaponizers
Attribution is in the object: using RTF object dimensions to track APT phishing weaponizers
Have you carried out research that furthers our understanding of the threat landscape? Have you discovered a technique that helps in the analysis of malware? The Call for Papers for VB2020 in Dublin is open until 15 March - submit a proposal now for a chance to make it onto the programme of one of the most international threat intelligence conferences!