Posted by Virus Bulletin on Jul 31, 2012
Downward trend in performance continues.
In the latest VBSpam comparative test of anti-spam products, 21 anti-spam solutions achieved a VBSpam award, but for the majority of products the spam catch rate showed a continuing decline.
We first reported this drop in March, and catch rates barely bounced back in May. The results of the July test showed another decline in most products' spam catch rates.
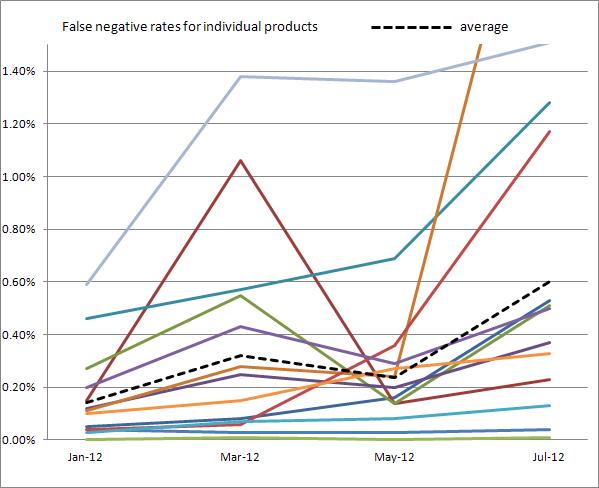
This perhaps becomes most clear when looking at the false negative rates (the measure of spam messages that were not blocked). We saw that, in March, the average false negative rate was about one in 700 spam messages. In July, this had decreased to one in 167 messages. (To avoid outliers influencing these averages, the highest and lowest scores were excluded from the calculation of the average.)
Over the last few years, botnet takedowns and policy changes at ISPs have seen the global volume of spam drop significantly. This is undoubtedly a good thing. But it has also forced spammers to look for other ways to make money from the emails they send - and improving their delivery rates is one thing they appear to have done.
It is important to realise that we haven't suddenly lost the war against spammers. We are still a very long away from the scenario of email accounts becoming unusable because of the vast amount of spam. Indeed, many products performed well in the recent test - and SpamTitan earned a 'VBSpam+' award by achieving a very high spam catch rate without missing a single legitimate email.
However, spammers have won an important battle and it is up to the anti-spam community to make sure this trend doesn't continue and, ideally, is reversed.
For Virus Bulletin subscribers the full test report is available here. Non-subscribers can purchase the standalone review ($19.95) here.
More on the VBSpam tests, including historical performance of the participating products, can be found here.
Posted on 31 July 2012 by Martijn Grooten