Posted by Virus Bulletin on Aug 12, 2014
75,000 jailbroken iOS devices infected with malware that steals ad revenues.
Believing that the device or operating system you use reduces your chance of being affected by malware is generally a bad idea, but those using iOS have the numbers on their side: malware targeting Apple's mobile platform is very rare.
But very rare doesn't mean non-existent. Today, we publish a paper by Axelle Apvrille, a researcher from Fortinet in France, in which she studies the iOS/AdThief malware.
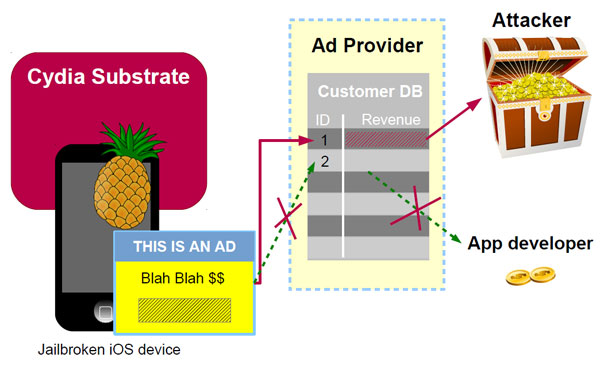
First discovered in March 2014, AdThief (or Spad, as its developers call it) has infected 75,000 devices. It uses the Cydia Substrate extension, which only works on jailbroken devices; hence so does AdThief.
AdThief uses Cydia Substrate to modify the developer ID sent when an advertisement is displayed or clicked, so that the revenue goes to the entity controlling the malware rather than to the legitimate advertiser. Axelle found 15 adkits targeted by the malware, eight of which are Chinese. It should be noted that jailbreaking mobile devices is a relatively common practice in China. An estimated 75,000 infected devices doesn't make the malware very prevalent, but with an estimated 22 million hijacked ads, it provides a decent amount of pocket money for the owners.
Using some debugging information that was left in the code, Axelle was able to deduce that the malware was written by a Chinese hacker, 'Rover12421'. He (or she) has confirmed having written part of the code, but denies having participated in the propagation of the malware.
You can download the paper here in HTML format, or here as a PDF (no registration required).
If you like this paper, you will be pleased to know that Axelle has regularly written for Virus Bulletin and spoken at the VB conference on various aspects of mobile malware. In July, we published a paper on the obfuscation of Android malware by Axelle and her colleague Ruchna Nigam: 'Obfuscation in Android malware, and how to fight back'.
Posted on 12 August 2014 by Martijn Grooten