Posted by Virus Bulletin on Oct 16, 2014
Nick Sullivan describes how DNSSEC uses cryptography to add authentication and integrity to DNS responses.
Over the next months, we will be sharing conference papers as well as video recordings of the presentations. Today, we have added 'DNSSEC - how far have we come?' by CloudFlare's Nick Sullivan.
It is rather scary to think about how much of the Internet depends on DNS, and how little guarantee that protocol provides about its responses being correct. The Kaminsky attack is well mitigated these days, but cache poisoning attacks do happen and there are various other ways in which the DNS response given may not be one that can ultimately be traced to the domain owner.
In his paper, Nick explains how DNSSEC uses cryptography to add authentication and integrity (but not confidentiality) to DNS responses, thus allowing DNS clients to trust the responses they receive from recursive name servers.
But DNSSEC could bring some bad news too: in its standard form, it allows an attacker to 'walk' a DNS zone, thus revealing all domains hosted on a nameserver, while the increased response sizes mean DNSSEC could be used for DNS reflection DDoS attacks.
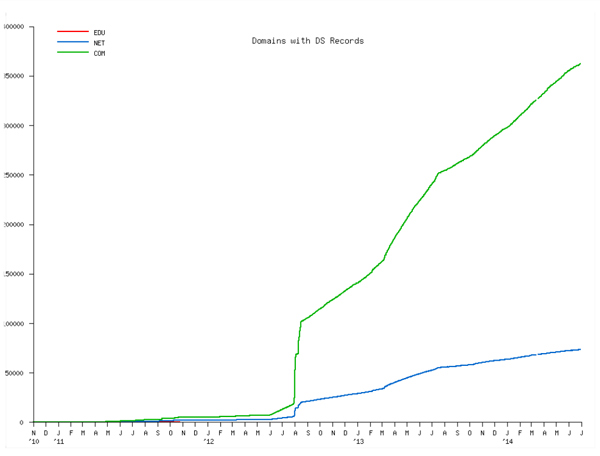
Moreover, key management comes with all sort of practical issues. Still, DNSSEC is a good thing and the fact that adoption is increasing (even if at a slow rate) is to be lauded.
You can read Nick's paper here in HTML-format, or download it here as a PDF (no registration or subscription required). You can download the presentation slides here. We have also uploaded the presentation to our YouTube channel.