Posted by Virus Bulletin on Oct 28, 2014
Cristina Vatamanu and her colleagues describe how botherders keep their C&C servers hidden.
Over the next few months, we will be sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added 'Hiding the network behind the network. Botnet proxy business model' by Bitdefender researchers Alexandru Maximciuc, Razvan Benchea and Cristina Vatamanu.
One of the most difficult parts of running a botnet is how to hide the command and control (C&C) servers. Early botnets used fixed IP addresses or fixed domain names, but that made them very vulnerable to takedowns by law enforcement or security researchers.
Modern botnets use more advanced techniques, such as domain generation algorithms (DGAs), Tor, or even fancy techniques such as Yahoo! Mail, but each of these has its own set of problems.
However, there seems to be no problem in cybercrime for which there aren't other cybercriminals who can provide a solution. In their paper, which was presented by Cristina Vatamanu in Seattle, Alexandru Maximciuc, Razvan Benchea and Cristina Vatamanu describe a proxy network that is rented to botnet owners for C&C communication.
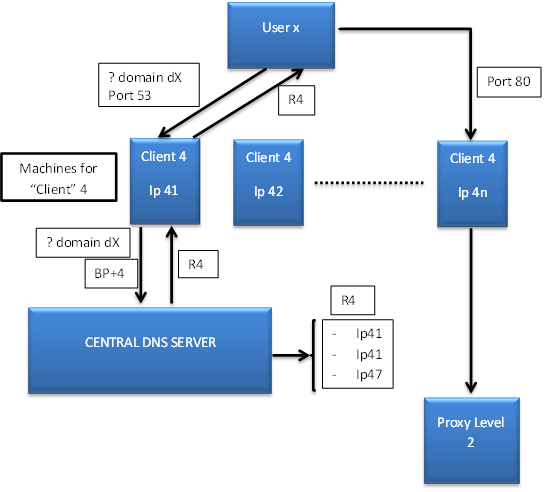
Using multiple layers, the proxy network (which is explained in full detail in the paper) is very cleverly designed. This didn't just make the botnet traffic hard to detect, it also frustrated the researchers' attempts to take down the botnet.
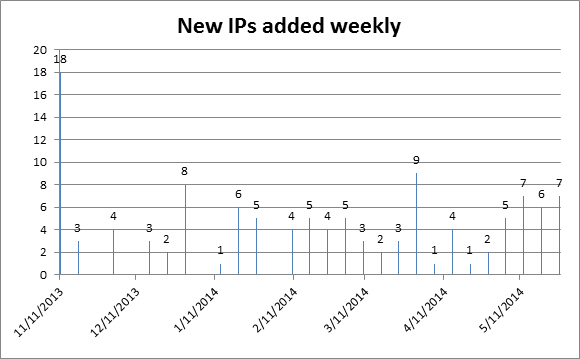
During their research, Cristina and her colleagues filed several abuse reports against IP addresses used in the proxy network. However, in all such cases the network was able to add different IP addresses very quickly.
Among the 'customers' of this botnet were 'Citadel' and 'CryptoLocker'. The former was the subject of a research paper we recently published (part 1, part 2), while in her presentation Cristina shared details of the researchers' attempts to disrupt the infamous CryptoLocker ransomware.
You can read the paper here in HTML-format, or download it here as a PDF (no registration or subscription required). You can download the presentation slides here. We have also uploaded the presentation to our YouTube channel.