Posted by Virus Bulletin on Oct 30, 2014
Malware spreads through infected torrent, then maintains persistence on the system.
A month ago, security firm Dr.Web reported it had discovered a new malware variant targeting Mac OS X, that was subsequently dubbed 'iWorm'.
Apart from the fact that malware for OS X, though becoming more common, is still a bit of a novelty, most reports focused on iWorm's unique way of obtaining a list of command and control servers: the malware performed a search on Reddit for a particular string, which was used by the owners of the botnet to post C&C addresses and ports.
Today, we publish a paper by Patrick Wardle, Director of Research at Synack, in which he performs a tactical study of iWorm, focusing on both the infection vector and the way the malware maintains persistence on an infected system.
Despite its name, iWorm is a backdoor and not a worm, and thus didn't spread automatically. Patrick explains how torrents of pirated versions of Adobe Photoshop and Microsoft Office were spread - which, apart from the promised program, also installed iWorm on the side.
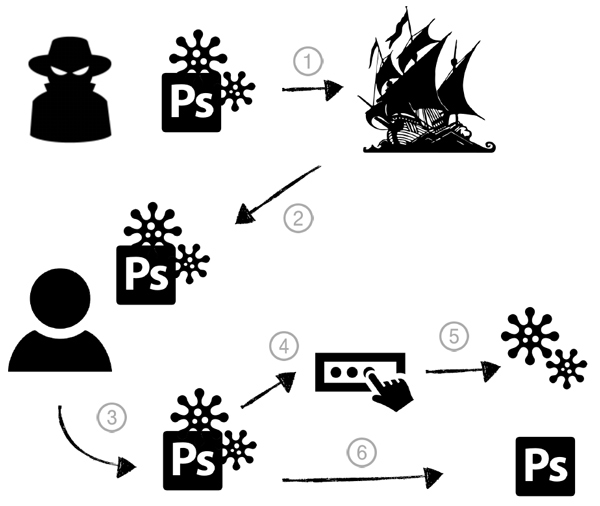
Once installed, the malware is executed automatically by the operating system every time the computer is restarted. There are many persistence methods on OS X, and iWorm uses a relatively simple method, by installing as a launch daemon.
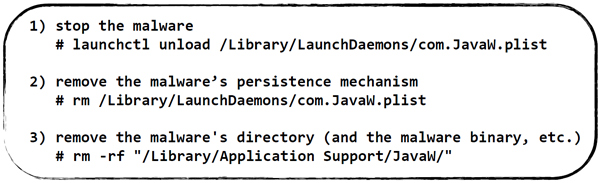
Thankfully, removing the malware is rather trivial and requires the execution of just three simple commands.
You can read the paper here in HTML format or here as a PDF. As always, papers published by Virus Bulletin are available free of charge and do not require registration.
If you are interested in the subject of persistence methods of OS X malware, you should read Patrick's VB2014 paper on the subject "Methods of malware persistence on Mac OS X", which we published this week. In it, he describes various persistence methods and also presents the KnockKnock tool, which one can use to find programs persistently installed on OS X.
Posted on 30 October 2014 by Martijn Grooten