Posted by Virus Bulletin on Nov 10, 2014
Developer Enterprise Program recently found to be used by WireLurker.
Over the next few months, we will be sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added 'Apple without a shell - iOS under targeted attack', by FireEye researchers Tao Wei, Min Zheng, Hui Xue and Dawn Song.
Considering its large user base, and given that malware targeting non-jailbroken devices can still be counted on the fingers of one hand, iOS is one of the most secure operating systems there is. Yet that doesn't mean there are no attack vectors.
In a paper presented by Tao Wei and Hui Xue at VB2014 in Seattle, the FireEye researchers look at an interesting vector that could be used to target iOS apps: the iOS Developer Enterprise Program.
This program allows companies to sign and distribute in-house apps that bypass Apple's famously strict review process. In particular, such apps are able to use private, undocumented APIs.
Not only are these undocumented APIs more powerful because they are not intended to be available to app developers, they are also not always designed with security in mind. Indeed, the researchers found a number of vulnerabilities, for instance one (CVE-2014-1276) that could be used to monitor a user's input - something that an attacker would certainly be interested in.
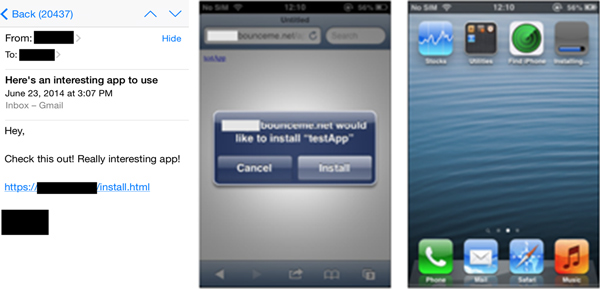
To obtain a certificate for the Developer Enterprise Program, all that is needed is $299 and a valid company - neither of which are beyond the means of an average attacker. Indeed, we saw last week how the 'WireLurker' attackers did just that.
This particular campaign also showed that Apple can and does revoke abused certificates, but in their paper, the researchers point out that an attacker could even block OSCP, the protocol that checks for revoked certificates, thus making the malicious app survive beyond the revocation.
You can read the paper here in HTML-format, or download it here as a PDF (no registration or subscription required). You can download the presentation slides here.
Posted on 10 November 2014 by Martijn Grooten